Is Filmyzilla.plus Safe? (Complete Virus Analisys)
Before we dive in
Before we dive in, let's make sure you stay safe online. We created SpyHunter because your security matters to us.
Protect your computer today — download SpyHunter right here! Check out our top tips below to keep your computer safe and secure.

Are you considering downloading content from Filmyzilla.plus but worried about its safety?
Navigating the murky waters of online streaming sites can be tricky, especially when it comes to protecting your digital security.
This article dives deep into the safety of Filmyzilla.plus, examining its legality, security risks, and potential consequences for users.
Stay tuned to uncover whether Filmyzilla.plus is a safe harbor for movie enthusiasts or a siren call best avoided.
Understanding Filmyzilla.plus website
Filmyzilla.plus is a website that may initially seem harmless but could present various concerns or doubts upon careful examination. It offers a variety of movies, including Bollywood, Hollywood, and Hindi dubbed films.
The true nature of the website is not transparent at first sight. This common characteristic of potentially unsafe platforms makes expanding on its weaves and intricacies necessary.
What is Filmyzilla.plus
Filmyzilla.plus is a website whose credibility has been questioned due to various factors, such as a lack of crucial security measures and a dubious reputation.
The platform offers full movies for download, including the latest releases.

Filmyzilla.plus security concerns
While any website, including Filmyzilla.plus, may appear harmless initially, evaluating its security measures is critical.
Many users access Filmyzilla.plus over the internet, often unaware of the associated legal risks and potential security threats. Many problems surround Filmyzilla.plus’s security practices, which raises questions about its safety.
These concerns range from an apparent lack of vital security components to susceptibility to data breaches and aggressive data collection methods.
Lack of vital security components
A key consideration is Filmyzilla.plus’s lack of essential security features such as SSL encryption and robust firewall protocols.
SSL encryption, denoted by ‘HTTPS’ in the URL bar, is a fundamental security measure employed by websites to protect sensitive user data.
A website lacking this essential component exposes users to potential data theft and unauthorized access to their data.
Similarly, the absence of sturdy firewall protections presents a significant vulnerability that could lead to potential data breaches.
Vulnerability to data breaches and unauthorized access
Due to the absence of vital security components, websites like Filmyzilla.plus become vulnerable to unauthorized access and data breaches.
Users could be redirected to unsafe third-party sites or be encouraged to download torrents from unreliable sources, which increases the risk of accidental malware installation or cyber threats.
Tracking and data collection methods
Apart from the potential data security breaches, Filmyzilla.plus may also use various cookies and tracking tools to collect user data.
Such practices could compromise user privacy as they involve intrusive data monitoring activities.
These could include tracking browsing history, keeping tabs on bookmarked websites, recording IP and MAC addresses, monitoring mouse movements, logging search queries, and collecting personal information users might enter.
These tracking mechanisms expose users to significant privacy risks.
Tip
If you suspect the presence of malware on your Mac and want a swift and reliable solution, consider using SpyHunter for Mac.
This advanced anti-malware tool is designed to detect and remove threats efficiently, ensuring your Mac stays secure and performs optimally.
Download SpyHunter for free here to enjoy sweeping Mac protection and peace of mind.
Estimating Filmyzilla.plus trustworthiness
Determining the trustworthiness of a website is a pivotal task when considering its safe usage.
Users can watch a variety of movies and TV shows on Filmyzilla.plus, but the site’s trustworthiness is questionable.
When a website like Filmyzilla.plus does not have a strong or noticeable reputation, various problems may arise, leading to questions about the site’s reliability.
Lacking a strong reputation or significant online presence
A website lacking solid standing or substantial online presence often raises red flags about its credibility. Filmyzilla.plus falls into this category, and its use should be cautiously treated.
A low online presence can indicate a new or poorly managed site, and the absence of a strong reputation often suggests past user dissatisfaction or untrustworthy behavior.
Risk of redirection to fraudulent or harmful sites
If suspicious activity like adware is detected in association with a website, in this case, Filmyzilla.plus, users have an increased risk of redirection to potentially harmful locations.
These could range from untrustworthy software download sites, fraudulent survey websites, and phishing pages to URLs that host virus-infected files or scripts and websites that host various scams.
Possible exposure to malvertising and associated crimes
Not only does Filmyzilla.plus’s questionable activity brings significant security risks, but it may also involve participation in “malvertising.”
This form of advertising uses online ads to spread malware, often redirecting users to unsafe sites via pay-per-click routes.
The risks associated with malvertising are significant and include malware infections such as ransomware, Trojans, and rootkits.
Alongside the high risk of malware, users may encounter tech support scams and phishing incidents, further enhancing the potential dangers of using Filmyzilla.plus.
Filmyzilla.plus virus analysis
Filmyzilla.plus, like many other public torrent websites, poses a significant risk to users’ devices and personal data.
The website’s lack of regulation and oversight creates an environment conducive to the spread of malware and viruses.
When users download movies or files from Filmyzilla.plus, they may inadvertently expose their devices to various types of malware, including:
- Trojans: These malicious programs can grant unauthorized access to users’ devices, allowing hackers to steal sensitive information or take control of the device.
- Ransomware: This type of malware can encrypt users’ files and demand payment in exchange for the decryption key.
- Adware: These programs can display unwanted advertisements, slowing down devices and compromising user experience.
- Spyware: These malicious programs can monitor users’ online activities and steal sensitive information such as login credentials and credit card numbers.
To avoid these risks, users should exercise extreme caution when visiting Filmyzilla.plus or any other public torrent website. It is essential to have up-to-date antivirus software and a reliable firewall to protect against potential threats.
Proactive measures against Filmyzilla.plus
Navigating the turbulent waters of potentially harmful websites like Filmyzilla.plus is a complex task that demands a clear understanding of their functionality and threat landscape.
To protect yourself and your device adequately, weighing the pros and cons of using such a site and considering the necessary precautions is beneficial.
Pros and cons of using Filmyzilla.plus
While the platform has not been identified as explicitly malicious, it carries several substantial negatives that are hard to ignore.
A lack of associated social media profiles limits the scope for user engagement and interaction.
The site may redirect users to unfamiliar and potentially harmful websites, and the possibility of the site using third-party cookies for data collection presents a significant privacy concern.
Additionally, users risk downloading harmful files that may lead to malware infections, and the likely encounter with similar risky websites further lowers the appeal of Filmyzilla.plus.
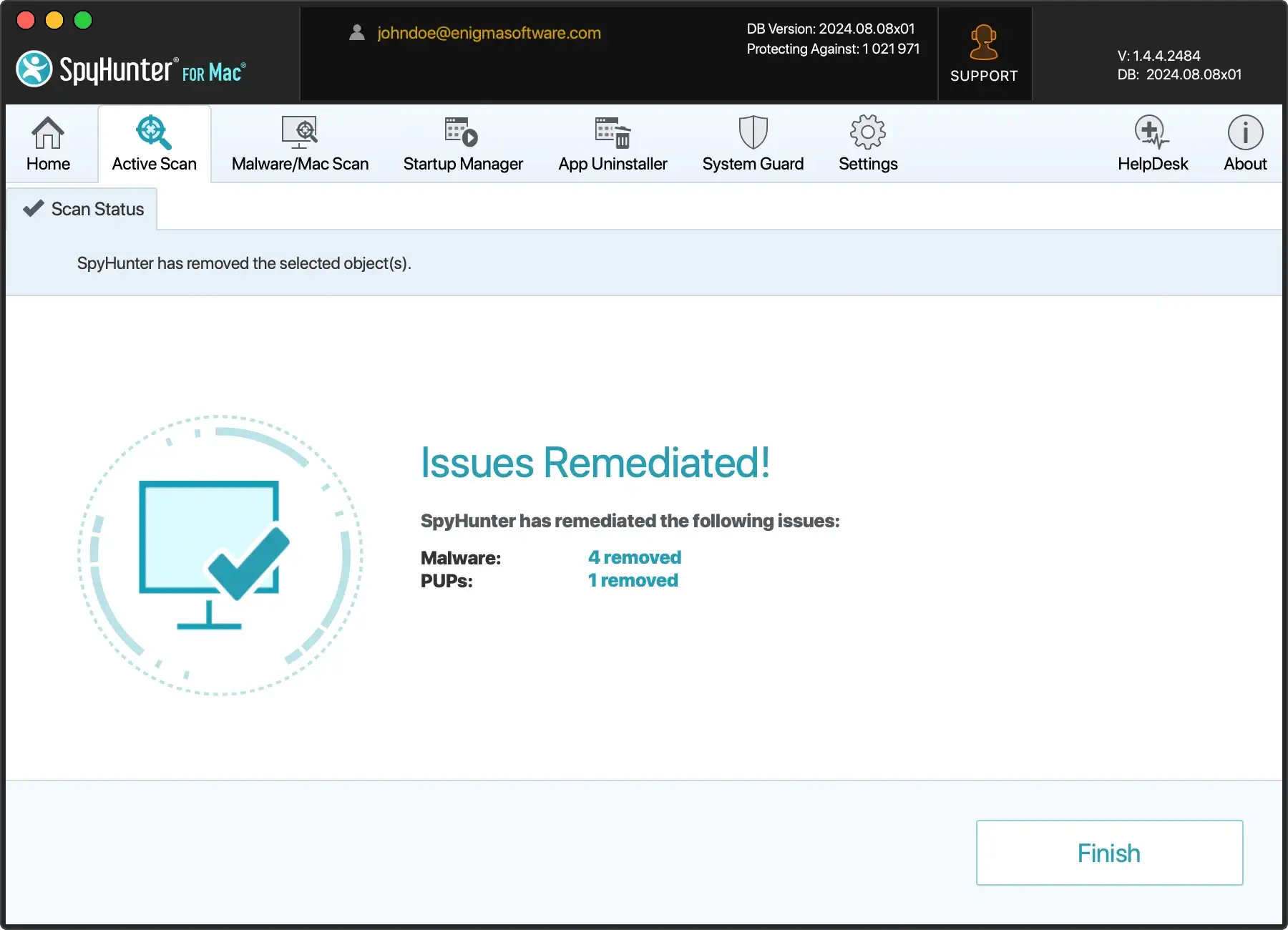
Use professional anti-malware software to protect your device
Experts recommend professional anti-malware software like SpyHunter for a comprehensive security solution. This tool can autonomously scan, detect, and remove any suspected malware from your device.
Running a scan before purchasing the full version of the software ensures that the tool detects the current malware version, further bolstering your device’s protection against sites like Filmyzilla.plus.
It’s advisable to check the corresponding links to gauge the performance of SpyHunter.
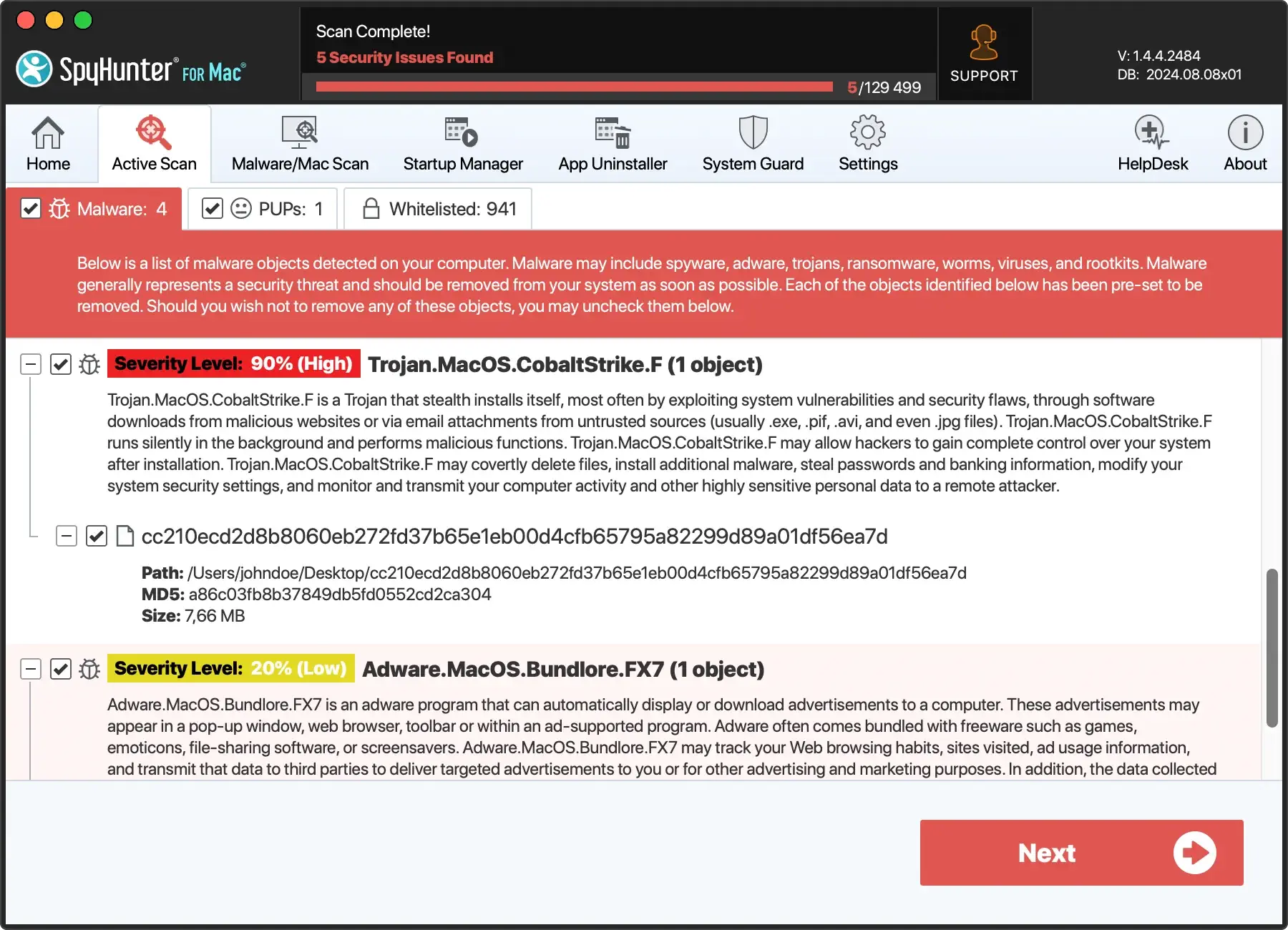
Cybersecurity experts recommend leveraging professional anti-malware software such as SpyHunter to safeguard your device effectively.
This advanced tool offers a comprehensive security solution by autonomously scanning, detecting, and removing suspected malware from your device.
Before purchasing the full version, you can initiate a scan to ensure that SpyHunter detects the current version of the malware, enhancing your device’s protection against threats from sites like Filmyzilla.plus.
- Download SpyHunter for free here and follow the on-screen instructions to complete the installation.
- Once installed, an automatic scan will identify any remaining malware on your Mac.
- Follow SpyHunter’s instructions to remove the threats, keeping your device malware-free.
Taking proactive measures with reputable anti-malware software adds a layer of defense to your device, ensuring a safer online experience.
Legitimate alternatives to Filmyzilla.plus
For users seeking to download or stream movies and TV shows, there are several legitimate alternatives to Filmyzilla.plus. These options offer a safer and more reliable way to access a wide range of content:
- Netflix: A popular streaming service offering a vast library of movies, TV shows, and original content.
- Amazon Prime Video: A streaming service providing access to a vast collection of movies, TV shows, and original content, including exclusive titles.
- Hulu: A streaming service offering a range of TV shows, movies, and documentaries.
- YouTube: A video-sharing platform featuring a vast collection of user-generated content, including movies, TV shows, and music videos.
- Google Play Movies & TV: A digital distribution platform offering a wide selection of movies and TV shows for rent or purchase.
- iTunes: A digital media player and online store offering a vast collection of movies, TV shows, and music.
These legitimate alternatives provide a safer and more reliable way to access a wide range of content without the risks associated with public torrent websites like Filmyzilla.plus.
Conclusion
In conclusion, Filmyzilla.plus is a public torrent website that poses significant risks to users’ devices and personal data. The website’s lack of regulation and oversight creates an environment conducive to the spread of malware and viruses.
While the website may offer a wide range of movies and TV shows for free, the risks associated with using it far outweigh any potential benefits.
Users seeking to download or stream movies and TV shows should consider legitimate alternatives, such as Netflix, Amazon Prime Video, Hulu, YouTube, Google Play Movies & TV, and iTunes.
These options provide a safer and more reliable way to access a wide range of content without the risks associated with public torrent websites like Filmyzilla.plus.
In summary, Filmyzilla.plus is not a recommended website for downloading or streaming movies and TV shows. Instead, users should opt for legitimate alternatives that prioritize user safety and security.