Remove MAAS Ransomware: Protect Your Mac Now
Before we dive in
Before we dive in, let's make sure you stay safe online. We created SpyHunter because your security matters to us.
Protect your computer today — download SpyHunter right here! Check out our top tips below to keep your computer safe and secure.

MAAS ransomware is a type of malware that encrypts files on a victim’s computer, adding the “.maas” extension to each file it encrypts.
As a result, the files become inaccessible to the user. It is associated with the STOP/DJVU ransomware family and demands a ransom to be paid in Bitcoin for the potential recovery of the encrypted files.
This article offers an in-depth analysis of MAAS’s mechanisms, impact, and strategies for prevention, equipping readers with essential knowledge to safeguard their digital environments against this malicious software.
MAAS Ransomware: A threat to Mac users
The MAAS ransomware belongs to the STOP/DJVU malware family. It has been notorious for its impact on Windows systems. By encrypting files with the “.maas” extension, it denies access and then demands a ransom to release the decryption key.
The implications of MAAS ransomware infiltrating the macOS ecosystem are substantial, warranting heightened vigilance and defensive measures from all macOS users to shield themselves from such evil attacks.
The technical details of MAAS
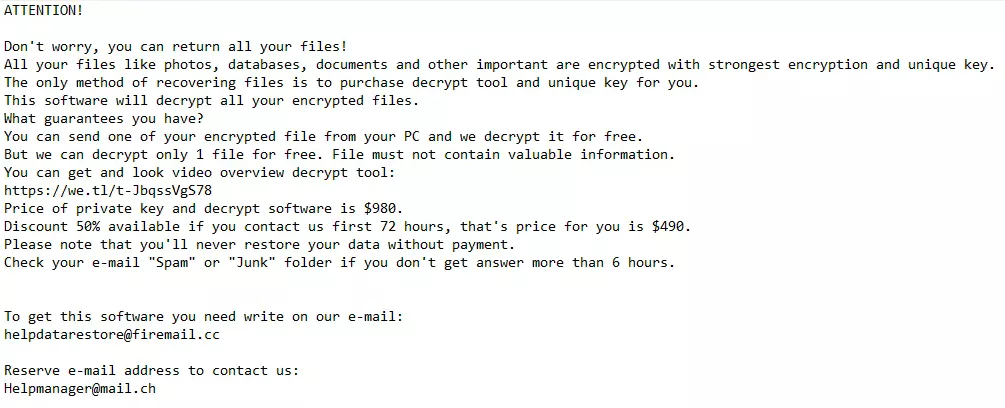
MAAS is characterized by its encryption method, which appends the “.maas” extension to infected files, rendering them inaccessible. The ransom notes, autogenerated in a “_readme.txt” file, instruct victims to contact the attackers via given email addresses to negotiate the payment for data recovery.
The encryption strength of MAAS ransomware is formidable, and without the decryption key, the affected files remain locked. Its association with the STOP/DJVU ransomware lineage suggests a robust and sophisticated malware strain, reinforcing its capacity to cause significant damage to personal data and system integrity.
Users should note that despite encryption strengths, the recommendation is to seek professional assistance rather than submitting to the ransom demands, as it does not guarantee the recovery of files and may further encourage cyber criminals.
How does MAAS ransomware infiltrate Mac?
The infiltration methods of MAAS ransomware are similar to those targeting Windows systems, often leveraging social engineering techniques and exploiting vulnerabilities.
Phishing emails masquerading as legitimate communications from reputable companies such as shipping firms are expected. These deceptive emails allure recipients into opening malicious attachments or links, initiating the ransomware infection.
Additionally, MAAS can exploit unpatched vulnerabilities in macOS or applications like browsers and Microsoft Office for Mac. It highlights the critical need for macOS users to maintain up-to-date systems and software, be wary of unsolicited email attachments and links, and adopt comprehensive security solutions to thwart such insidious threats.
Initial steps to take after MAAS ransomware infection
Upon discovering a MAAS infection, acting swiftly to mitigate further damage is imperative.
The initial steps involve creating a secure backup image of the encrypted drives, which may be crucial for potential data recovery processes later on. Before delving into malware removal procedures, confirm that all steps are followed sequentially to avoid complications.
If uncertainty or questions arise during the removal process, seeking expert assistance is advised to ensure the security and integrity of your system.
Isolate your Mac to prevent further spread
To stop the MAAS ransomware from propagating across your network or to other devices, immediately isolate your infected Mac.
This involves disconnecting it from the internet, turning off Wi-Fi and Bluetooth connections, and unhooking shared network drives. Furthermore, avoid using external storage devices like USB drives, as they can become vectors for the ransomware to spread.
Isolation is a critical containment measure that helps safeguard other systems and data while you address the infection on the compromised device.
Identify the ransomware: Signs and symptoms of MAAS
Symptoms of a MAAS ransomware infection are not subtle: you will notice that documents, images, and videos now have a “.maas” extension and are inaccessible.
The malware indicates its presence through a ransom note titled “_readme.txt” on the desktop. This note is a distinct sign of ransomware activity, and it will contain instructions for payment and contact details for cybercriminals.
Recognizing these signs promptly can aid in quicker response actions and may minimize the harm inflicted by the ransomware.
Remove MAAS ransomware: A comprehensive macOS guide
Confronting the threat posed by MAAS ransomware on macOS requires a multi-faceted approach. A thorough removal strategy eradicates the infection and lays the groundwork for robust preventative measures to avoid future incidents.
Given the complexities often associated with ransomware removal, the outlined steps aim to provide clear guidance through the process, underscoring the necessity of attending to every detail to ensure the complete removal of the MAAS ransomware from your system.
STEP 1: Utilizing Mac-Specific Malware Removal Tools
For Mac users, combating MAAS ransomware begins with deploying specialized malware removal tools tailored for macOS.
SpyHunter for Mac emerges as a paramount choice, offering comprehensive detection and removal capabilities for a broad spectrum of malware, including the MAAS ransomware.
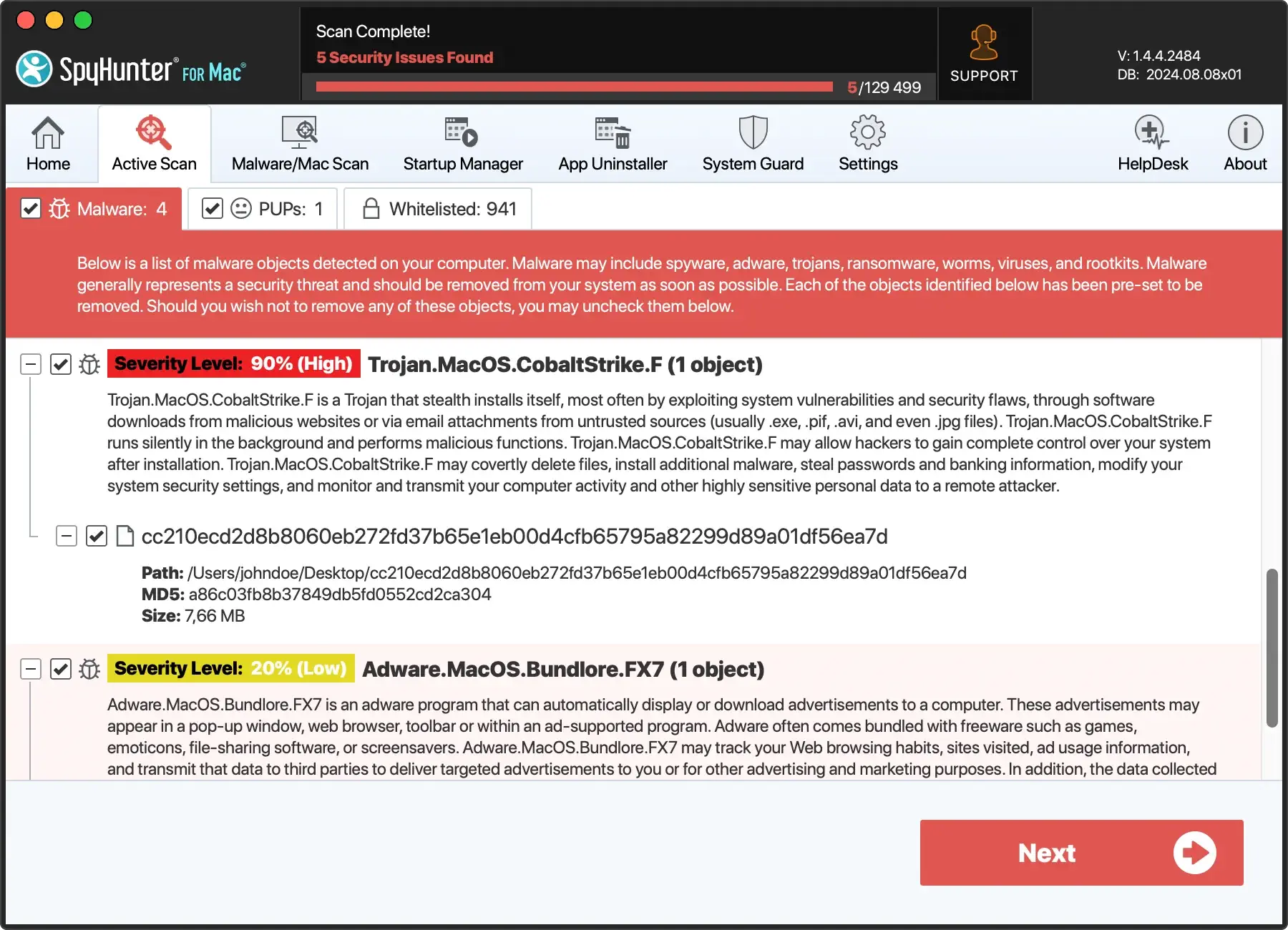
Initiating a full system scan with SpyHunter can efficiently identify and eliminate the malicious entities hiding within your system.
Download SpyHunter for free here to ensure the integrity and security of your device.
STEP 2: Advanced techniques to remove MAAS ransomware
If essential removal tools fall short, advanced techniques become necessary. This includes manual searches and deleting ransomware-related files or processes via the macOS Terminal. Exercise caution in the Terminal to avoid unintended system damage.
Familiarity with macOS’s file system is crucial for effectively identifying and removing disguised malicious files.
STEP 3: Secure your Mac with a comprehensive antivirus solution
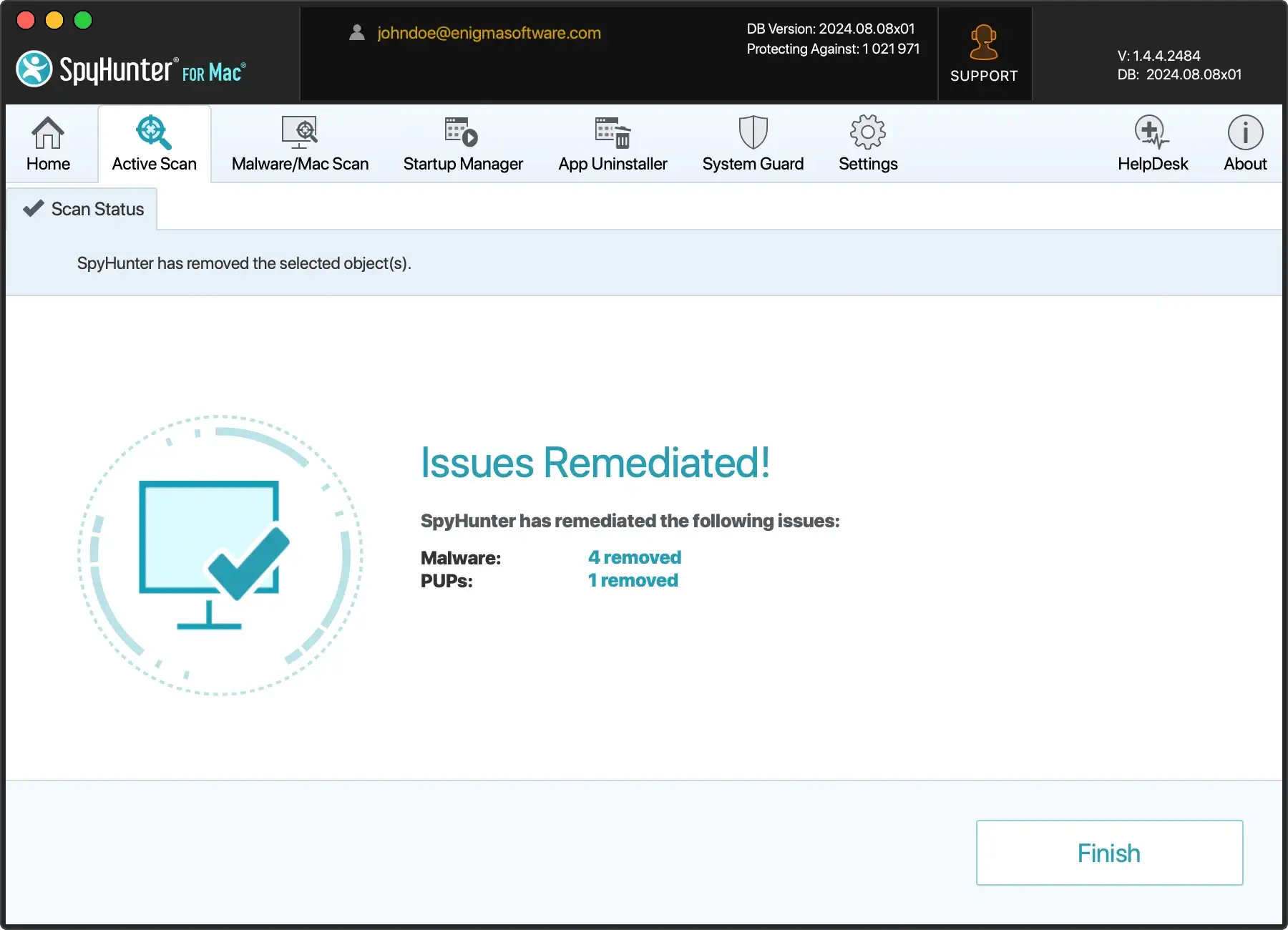
Completing the MAAS ransomware removal process requires additional security measures. SpyHunter for Mac stands out, equipped with auxiliary scanning and advanced System Guards features.
SpyHunter identifies and eradicates the immediate threats by initiating a comprehensive system scan. Additionally, the System Guards proactively block the execution of malicious processes, offering an additional layer of defense against MAAS ransomware and other malware threats.
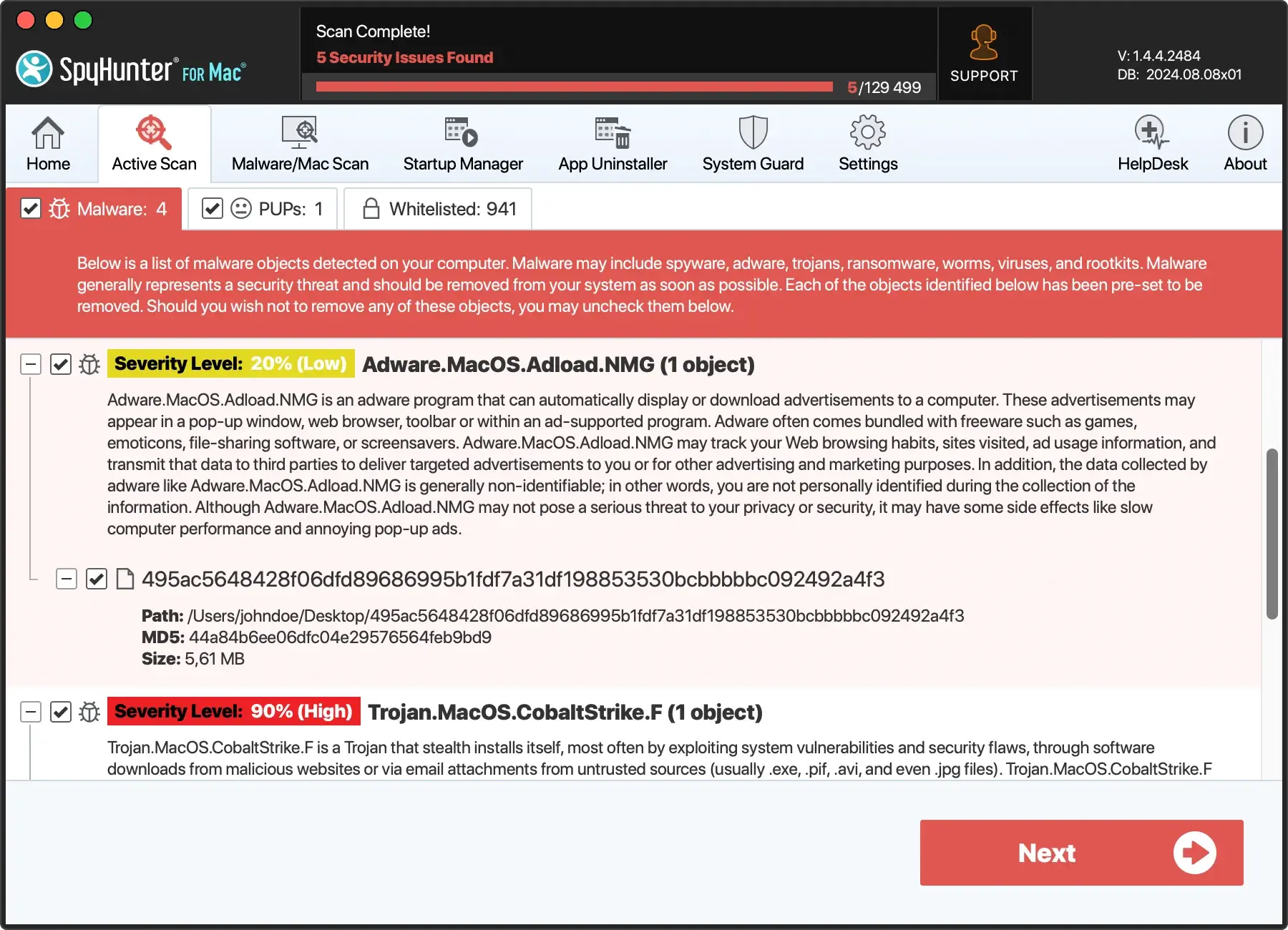
- Download SpyHunter from here and follow the installation instructions.
- Perform a complete scan of your Mac and remove any detected threats.
- After the scan, activate SpyHunter’s System Guards to protect your Mac from future malware intrusions.
Mac users can adopt a strategic and vigilant approach to removing MAAS ransomware by following these steps.
Integrating SpyHunter for Mac into your cybersecurity regimen not only aids in the immediate removal of MAAS but also strengthens your overall digital protection strategy.
Recover MAAS-encrypted Mac files
Understanding the MAAS ransomware’s encryption mechanism is crucial for considering appropriate recovery tactics.
Unfortunately, sophisticated encryption often leaves victims with limited options for recovering their files. Mac users face the additional challenge of finding compatible solutions with their operating system.
The options for attempting file recovery often involve exploring decryption possibilities, utilizing built-in Mac features like Time Machine for backups, and considering professional data recovery services that may come at a high cost but offer a chance for restoration.
Method 1: Decryption possibilities for .maas encrypted files
Decryption is typically the most desired solution for recovering files encrypted by ransomware.
For Mac users impacted by MAAS, the first step involves verifying whether the encryption was of the offline or online variety. This distinction is vital because offline encrypted files have a slightly better chance of decryption if security researchers capture the necessary key.
To check your MAAS encryption type, Mac users can locate the PersonalID.txt file, if available, and see if their unique ID ends in ‘t1’, which signifies offline encryption.
Method 2: Leveraging Time Machine for Mac data recovery
Time Machine, the built-in backup feature on Macs, can be a lifesaver in ransomware situations. If the user has a habit of performing regular backups with Time Machine, restoring files to a point before the ransomware infection occurs is possible.
To do this, users should navigate to the Time Machine application after ensuring their Mac is ransomware-free and select the most recent backup date before the ransomware attack. It’s critical to confirm that the system is clean before restoring to prevent the ransomware from affecting the freshly restored files.
Method 3: Professional data recovery services: worth the cost?
When all else fails, and if the data encrypted by the MAAS ransomware is vital, Mac users might consider turning to professional data recovery services.
These services often come with steep fees, and there’s no guarantee of success, especially when dealing with advanced encryption like MAAS. However, professionals may have tools or methods that are not publicly available and might stand a chance to recover some data.
Users should research and select respected data recovery firms, ideally those with a proven track record of handling ransomware cases. It’s also advisable to consult these professionals before making any payment to understand the potential for success and the cost involved in the recovery process.
Secure your Mac from future ransomware attacks
Update your macOS and security software regularly
Protecting your Mac from future ransomware and malware threats begins with updating the macOS and security software.
Regular updates bring new features to your devices and patch known vulnerabilities that cybercriminals exploit. Enable automatic updates to ensure you’re always running the latest versions, and periodically check for manual update notifications.
Best practices for macOS users to avoid ransomware
- Use Strong Passwords: Ensure all your online accounts and Mac logins have solid and unique credentials, preferably managed by a password manager.
- Enable Firewall: Turn on the macOS built-in firewall to provide an extra layer of protection against unauthorized access.
- Limit Administrative Privileges: Use a non-administrative account for everyday tasks, only using an admin account when necessary to minimize the potential damage from malware.
- Install Security Extensions and Tools: Consider using browser security extensions and privacy tools to prevent malicious scripts from running in your web browser.
- Educate Yourself: Be aware of standard ransomware delivery methods, such as phishing emails and compromised websites, to avoid clicking on anything suspicious. Additionally, follow security experts and reputable sources to stay informed about the latest threats and advice on protecting your digital environment.
FAQs: Common concerns about MAAS ransomware
How does MAAS ransomware spread on computer devices?
MAAS ransomware can infect computers by leveraging spam email campaigns with infected attachments or links. It also exploits vulnerabilities in the operating system or installed software, such as browsers and Microsoft Office applications.
Can MAAS ransomware affect both individual and business users?
Yes, MAAS ransomware can affect both personal and enterprise users. Businesses are often targeted due to the potential for larger ransom payments and more valuable data, but individuals are also at risk, especially if they lack proper cybersecurity practices.
What should you do if your Mac is infected with MAAS?
If your computer is infected with MAAS ransomware, you should immediately isolate the infected machine from any networks to prevent further spread. Do not pay the ransom, as this does not guarantee that your files will be recovered and can encourage different criminal activity.
Instead, seek professional advice and report the ransomware to the relevant authorities in your country.
What are the signs that your computer might be infected with MAAS ransomware?
Signs that your device might be infected with MAAS include files that can no longer be opened with a “.maas” extension, a ransom note “_readme.txt” present on the desktop with instructions for payment, and possibly a slowdown of your computer as the malware encrypts your files.
How much is the ransom for MAAS ransomware?
The ransom amount demanded by MAAS typically ranges between $490 to $980 in Bitcoin. The sum might be doubled if unpaid within a specific timeframe (usually 72 hours from the infection).
What should be the next steps after a MAAS ransomware attack?
After a MAAS ransomware attack, you should first secure a backup of the encrypted files and remove the malware from your system.
Using reputable malware removal tools like SpyHunter can help to identify and eliminate the infection ( Download SpyHunter from here ).
After ensuring the malware is removed, explore recovery options for your encrypted files, which may include professional data recovery services or looking for available decryption tools if they exist.
Is it possible to decrypt files encrypted by MAAS without paying the ransom?
Decrypting files without paying the ransom can be challenging, especially if there is no known flaw in the ransomware’s encryption algorithm or if cybersecurity researchers have not made a decryption key available.
In some instances, if the ransomware used an offline key for encryption, there may be hope for future decryption tools, but there are no guarantees.
How can you protect your device from future MAAS ransomware infections?
To protect your Mac from future ransomware attacks like MAAS, ensure that you have updated cybersecurity software installed, avoid opening suspicious email attachments or links, keep your operating system and programs up-to-date, and regularly back up your important data.
Is reporting a MAAS ransomware infection important?
Yes, reporting a MAAS infection helps authorities track and combat cybercrime, and it may also assist in the potential recovery of your files if a solution becomes available.
Victims must report the attack to the appropriate government or cybersecurity organizations.