Remove ProType Browser Hijacker [Instructions Included]
Before we dive in
Before we dive in, let's make sure you stay safe online. We created SpyHunter because your security matters to us.
Protect your computer today — download SpyHunter right here! Check out our top tips below to keep your computer safe and secure.

ProType is a browser hijacker that silently infiltrates your system, altering your homepage and default search engine settings without permission. This invasive software forces unwanted redirects, often leading users to suspicious websites.
This guide thoroughly explores ProType. It details its impact on your browsing experience, the methods it employs to gain control over browsers, and provides practical strategies for its removal.
Discover how to safeguard your online navigation and ensure a ProType-free browsing environment.
Understanding ProType browser hijacker
ProType is a browser hijacker that changes your browser’s settings without your approval. It targets homepage settings and default search engines, leading to unwanted redirects to specific sites, including ProType.
ProType browser hijacker promotes the protype.com fake search engine by modifying browser settings.
Commonly, it affects popular web browsers like Google Chrome, Mozilla Firefox, and Safari by altering their home page, adding a new tab window, and default search engine settings.
How ProType gets installed
ProType stealthily infiltrates systems, often hitching a ride with freeware or shared software downloaded from the internet.
Unwary users opting for the ‘express’ or ‘recommended’ setup of other software may inadvertently grant permission to install ProType and other unwanted applications.
Understanding these concealed entry points is crucial for users seeking to prevent inadvertent installations and maintain control over their system’s integrity.
Symptoms of ProType installation
Detecting ProType on your device involves recognizing key symptoms that manifest upon installation. If ProType has taken residence in your system, you’re likely to observe the following:
- Frequent browser redirects to protype.com.
- Unauthorized changes to your browser’s homepage.
- A barrage of unwanted advertisements.
These conspicuous signs serve as red flags, prompting users to take swift action against the intrusive presence of ProType.
Effects of ProType on your browser
The ramifications of a ProType-infected browser extend beyond mere inconvenience. Once it hijacks your browser, ProType unleashes a cascade of disturbances.
It manipulates search results, injecting promotional content that compromises the authenticity of your online searches. The browser is plagued with:
- Sudden and undesired redirects that disrupt the seamless flow of your internet experience.
- Sluggish responses and hindering overall efficiency.
Perhaps more concerning is the heightened vulnerability it introduces – exposing your system to potential risks from other harmful programs and posing a threat to your data privacy.
Users must grasp the multifaceted consequences of ProType, fostering a proactive approach towards removal and fortification against future infiltrations.
Remove ProType browser hijacker
Removing the ProType browser hijacker involves several crucial steps. Each step should be followed carefully and systematically to ensure successful removal.
If you encounter difficulties or uncertainties during removal, seek professional assistance immediately.
Step 1: Delete malicious configuration profiles
Configuration profiles on your Mac dictate various settings and preferences, affecting your device’s operation.
The ProType browser hijacker may install such profiles to lock down your browser settings, making reverting unwanted changes challenging.
Removing these malicious profiles is a critical first step in regaining control. Follow these steps to locate and eliminate any harmful profiles installed by ProType:
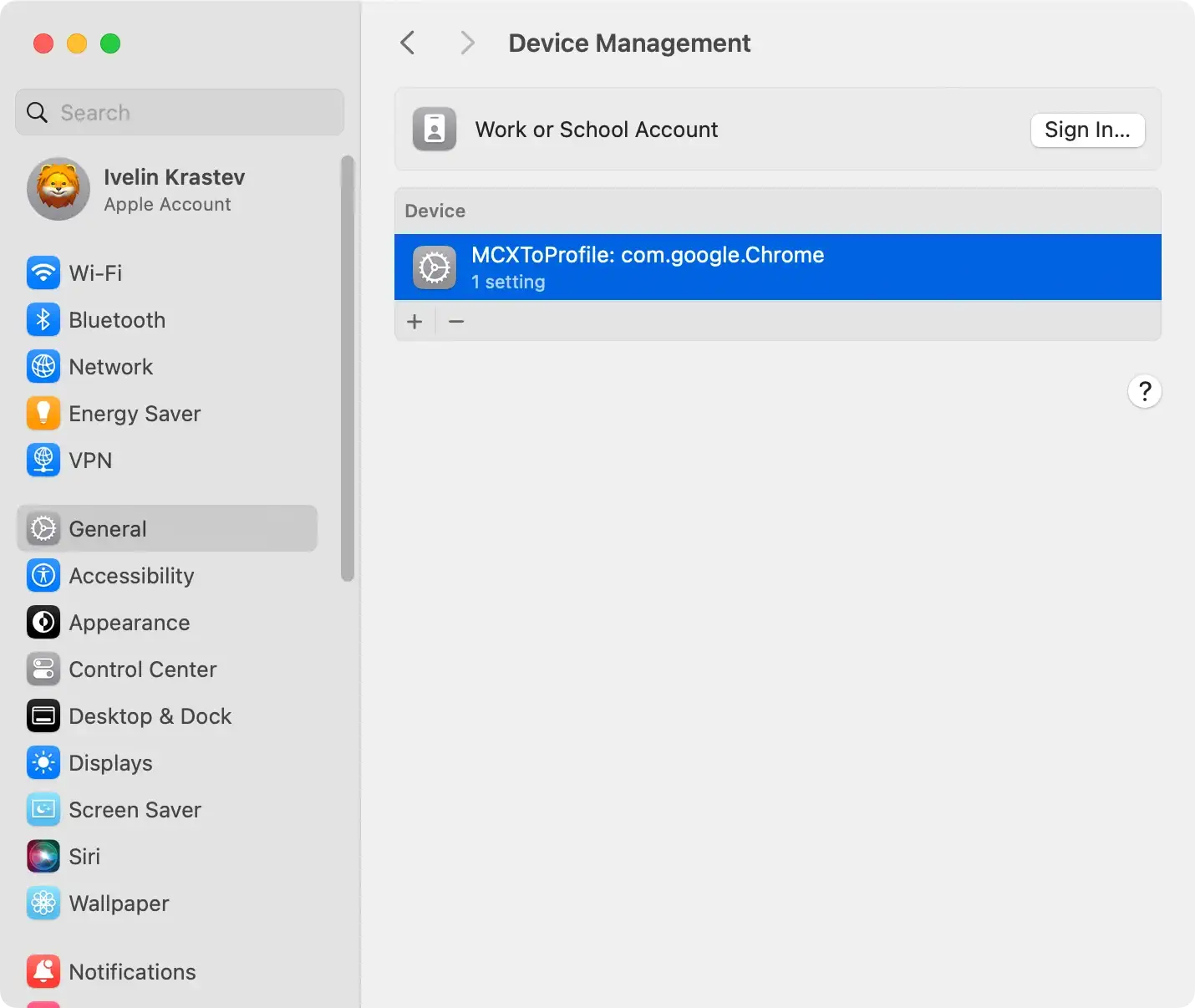
- Click on the Apple logo at the top left corner of your screen and select
System Preferences(namedSystem Settingson newer macOS versions). - Scroll down to find the
Profilesoption. If you don’t see it, no configuration profiles are installed on your Mac, which is typical for personal devices not managed by organizations. - Look through the list of profiles for any that you don’t recognize or seem out of place. Profiles installed by ProType may have unusual names or descriptions that don’t match legitimate applications or services you use.
- Select any suspicious profile and click the minus (-) button to delete it. You may be asked to enter your administrator password to confirm the removal.
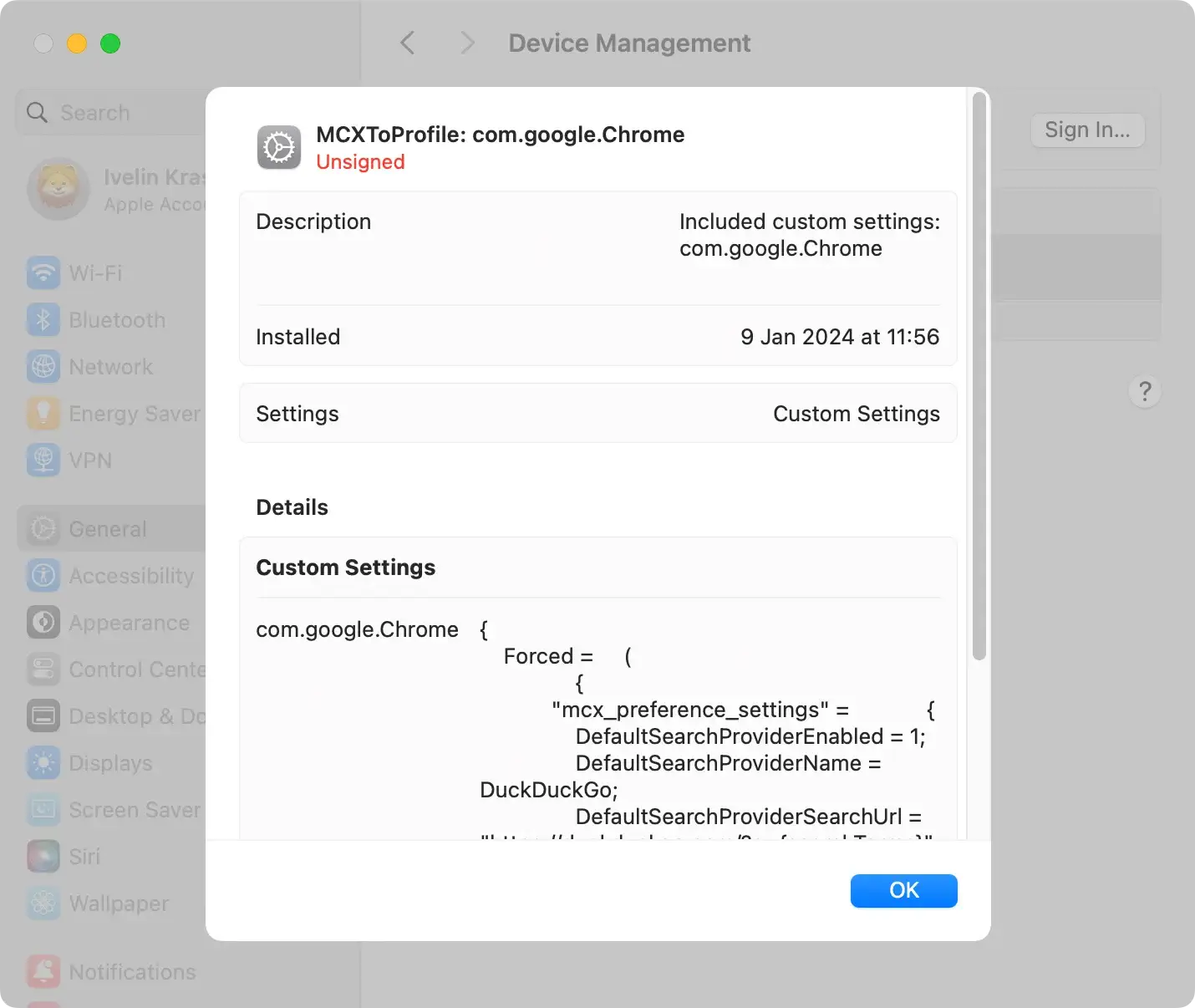
By meticulously following these steps, you effectively remove the grip ProType may have on your browser settings through configuration profiles, setting the stage for a cleaner and more secure browsing experience.
Step 2: Remove ProType-related applications
The second crucial step to remove ProType is to delete associated applications from your Mac. Follow this step-by-step guide to ensure thorough removal:
- Open
Finderand access theApplicationsfolder on your Mac. - Scan the folder for any instances of ProType or programs that seem suspicious. Pay attention to unfamiliar or recently installed applications that may be linked to ProType.
- Upon identifying a ProType-related application, right-click on it and choose the
Move to Trash/Binoption from the context menu. This action sends the application to theTrash/Bin, initiating removal. - To complete the removal, empty the Trash. Confirm the action when prompted. This step ensures that you have permanently removed ProType-related applications from your system.
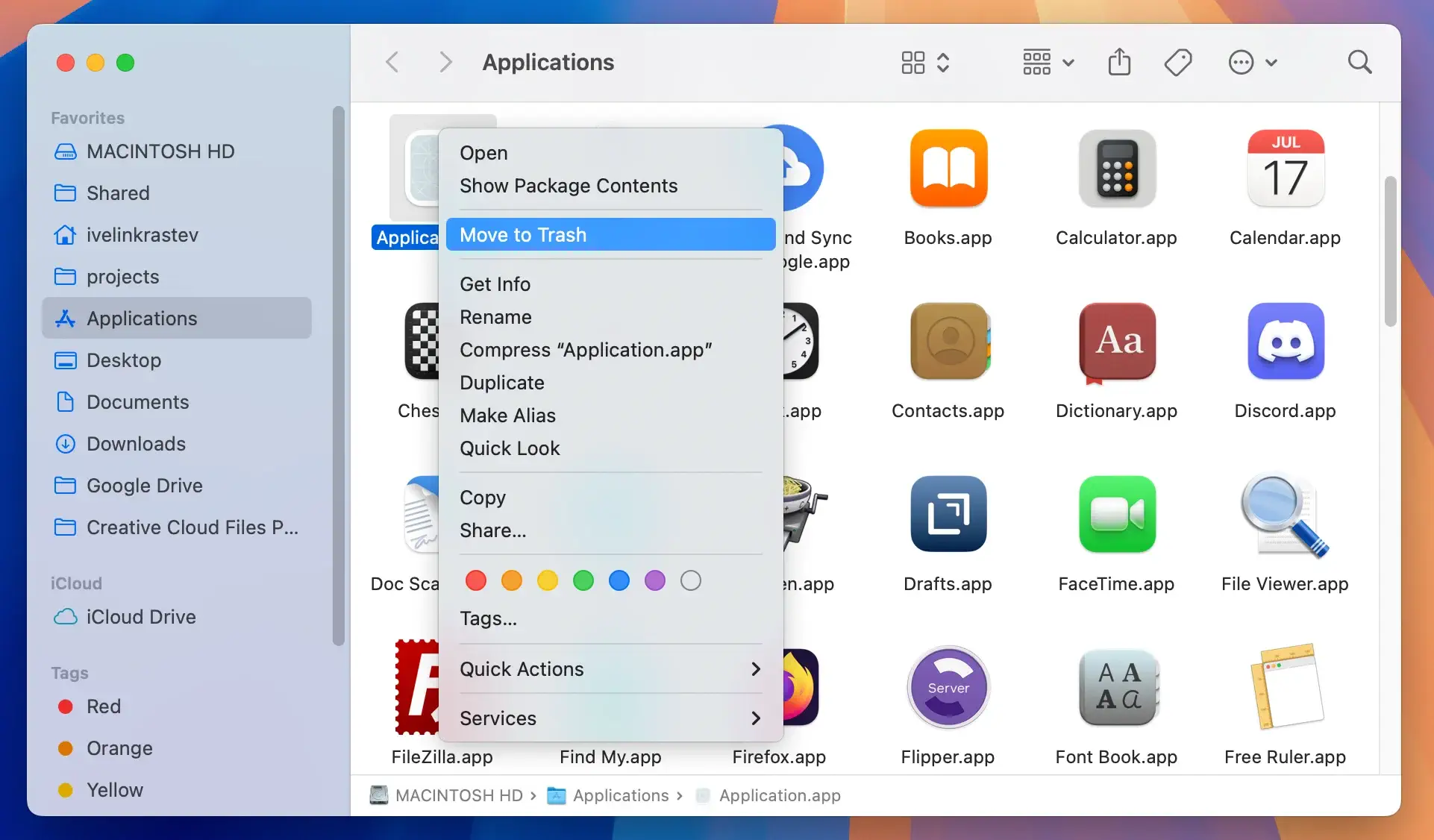
By meticulously executing these steps, you aim to eradicate ProType and restore control over your browser settings.
Remember to proceed cautiously and remove applications you are confident are associated with ProType to avoid unintended consequences.
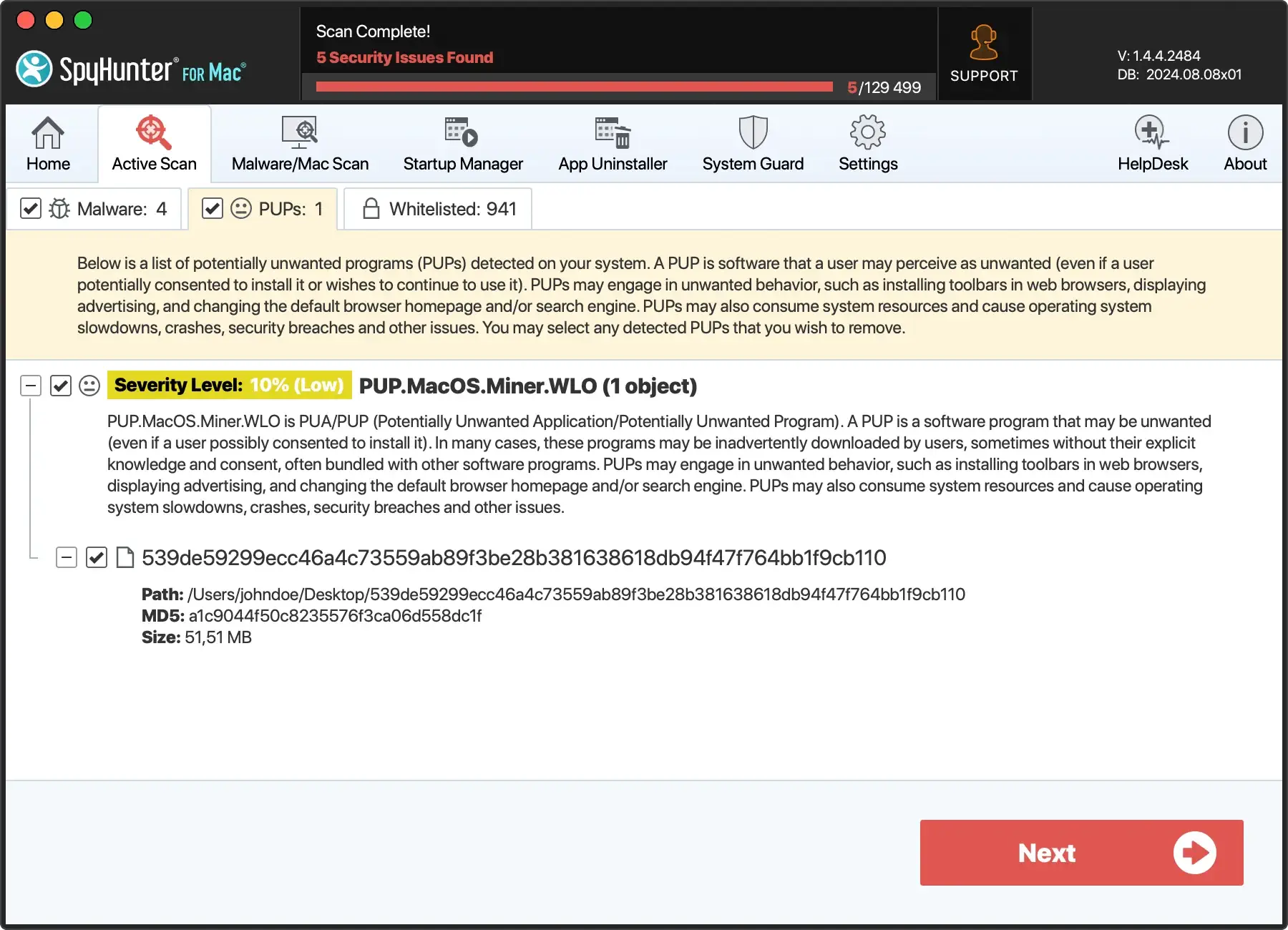
Step 3: Perform a full anti-malware scan on your Mac
After removing malicious profiles and applications, the next crucial step is ensuring no ProType remnants linger on your Mac.
Conducting a comprehensive anti-malware scan with a reliable tool like SpyHunter for Mac is essential.
SpyHunter for Mac is designed to detect and eliminate many malware threats, including stubborn browser hijackers like ProType.
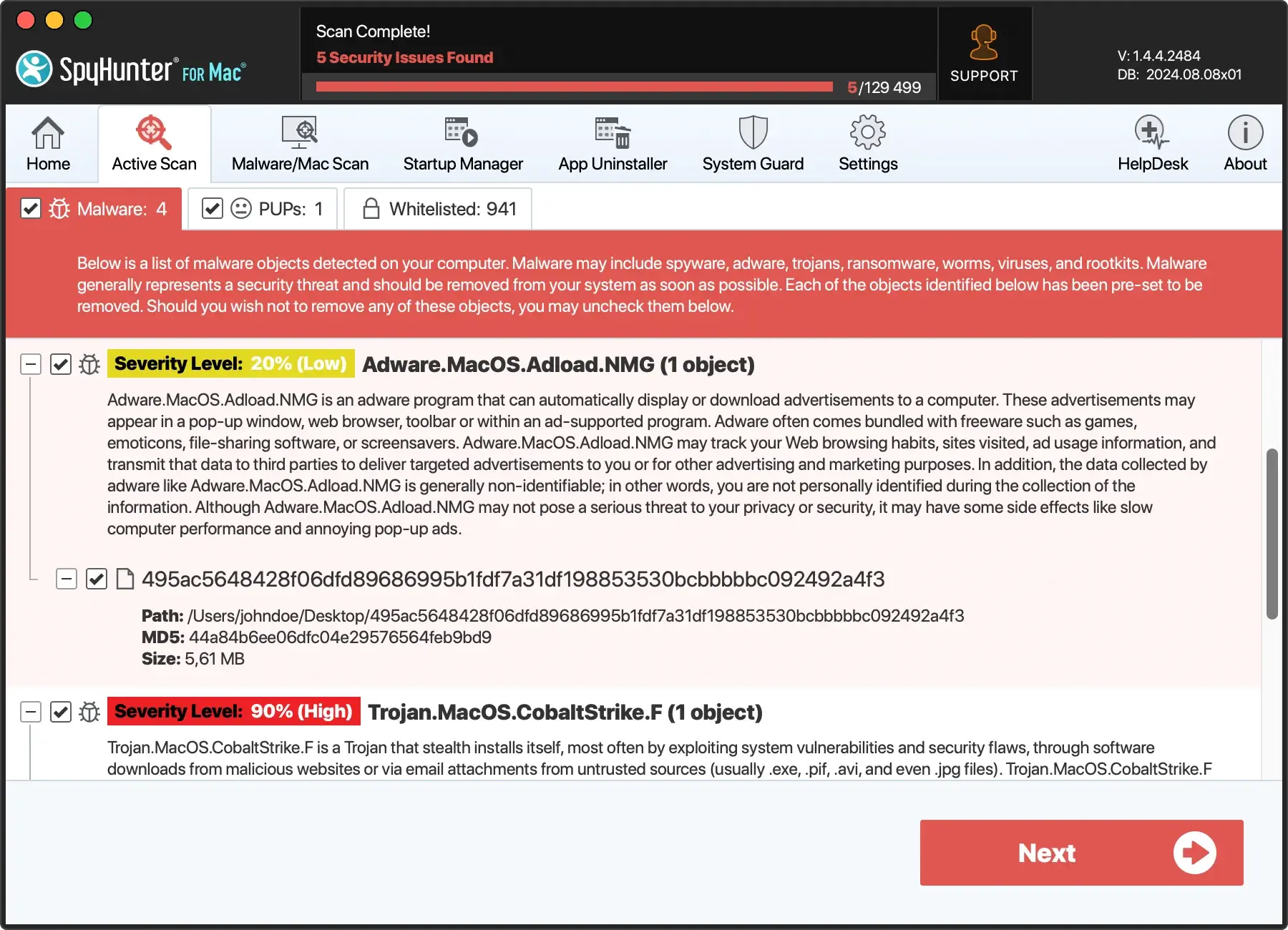
Its thorough scanning identifies hidden malware components, ensuring a clean slate for your system.
To get started with SpyHunter for Mac:
- Download SpyHunter from here to ensure you have the latest version of the app.
- Open the downloaded file and follow the on-screen instructions provided by the installer. The installation process is straightforward, guiding you through the steps to get SpyHunter up and running on your Mac.
- Upon installation, SpyHunter automatically begins a scan of your Mac. This scan is designed to identify any malicious entities, including any components of the ProType browser hijacker.
- After the scan is completed, SpyHunter presents a list of detected threats. Review these findings and use the software to quarantine the identified malware.
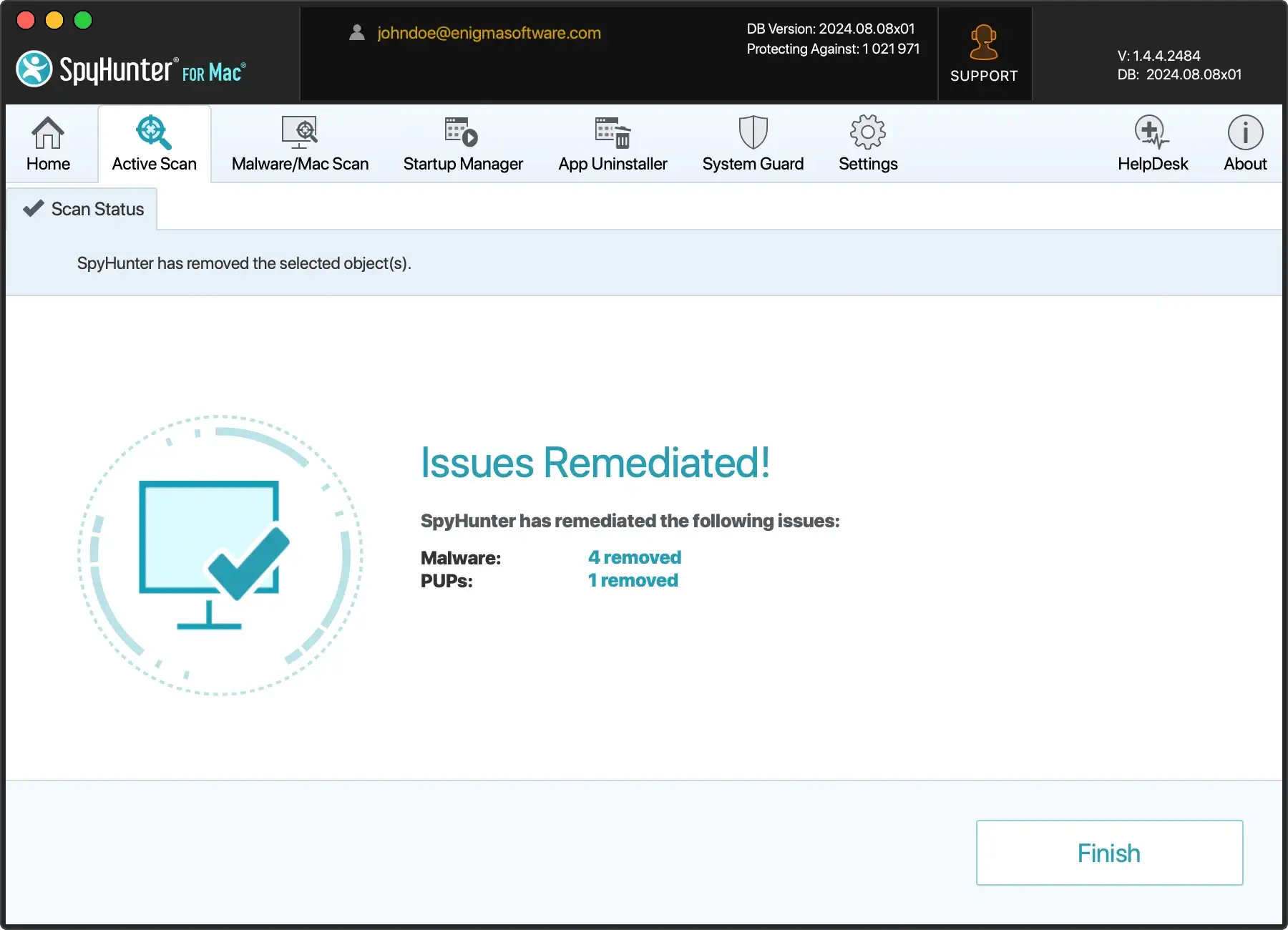
By following these steps and utilizing SpyHunter for Mac, you can confidently remove ProType and other malicious software, safeguarding your Mac against future threats and ensuring a secure browsing experience.
Step 4: Remove ProType from Safari, Chrome, or Firefox
Browser hijackers often leave lingering traces in these applications, causing disruptions and compromising your online experience.
Follow the step-by-step instructions below to ensure a thorough cleanup, restore the integrity of Safari, Chrome, or Firefox, and bid farewell to the intrusive presence of ProType.
Remove ProType from Safari
To remove any suspicious extensions on Safari:
- Go to the Safari menu, choose
Preferences, then click theExtensionstab. - Look through the list for extensions you don’t recognize or seem suspicious.
- Select any unknown or suspicious extensions and remove them.
- Navigate to the
Generaltab within thePreferenceswindow. You can set your preferred homepage by typing the URL into the homepage field. - Move to the
Searchtab in thePreferenceswindow. Choose your preferred search engine from the dropdown menu.
Remove ProType from Google Chrome
To bring Chrome back to its default settings:
- Open Chrome Settings: Click on the three vertical dots at the top right corner of the Chrome window and open the settings window.
- Access Extensions: Click on the three horizontal lines beside Settings at the top left corner and choose the
Extensionsoption. Browse through the list of extensions. - Remove Suspicious Extensions: For any extensions that appear suspicious or unfamiliar, click the option to delete them.
- Review Changed Settings: If ProType has altered your Chrome settings, inspect various settings that may have been modified without your consent. Manually revert any changes to restore your preferred configurations.
Remove ProType from Mozilla Firefox
To revert Firefox to its defaults:
- Type
about:supportin the Firefox search bar and press Enter. - Click
Refresh Firefox…on the right side of the page. Firefox will save your essential information and reset the rest to default settings. - After the refresh process, a window will display the imported data. Click the
Finishbutton, and Firefox will restart. - Post-refresh, Firefox places old data into a folder named
Old Firefox Dataon your desktop. If the reset doesn’t fix the issue, you might find this folder helpful for recovery.
Final steps and recommendations
ProType adware, like any other intrusive software, requires strict measures to eliminate it from your device and to protect it from similar attacks in the future. Here are some final steps and recommendations to follow.
Deal with any leftover issues
Take immediate action if you notice any residual changes in your browser or computer settings after removing the ProType adware.
Address fake warnings and ignore alarming pop-ups purportedly detecting a virus on your computer. It’s also recommended to store sensitive data like usernames, passwords, and credit card details in a password manager to keep it encrypted.
Additionally, establish a regular backup system using tools like Time Machine to recover your system or specific files if they become corrupted.
Use strong antivirus protection
In an era where the threat landscape continually evolves, reinforcing your system’s defenses with strong antivirus protection becomes essential.
Antivirus software stands as a brave guardian against the ever-growing sophistication of malware, providing a crucial line of security for your digital environment.
As a recommendation, consider employing a trusted solution such as SpyHunter – a powerful antivirus tool designed to combat a spectrum of threats.
- Download SpyHunter for free here and follow the on-screen instructions to complete the installation.
- Launch SpyHunter and let its advanced scanning capabilities identify and neutralize potential security risks, ensuring comprehensive protection for your system.
By embracing SpyHunter’s proactive shield, you empower your system to navigate the digital landscape with enhanced resilience against emerging security threats.
Download now and elevate your defense mechanisms to a level that goes beyond the ordinary.
Be careful during software installation
It’s crucial to pay attention during software installation because often, a software installer includes optional installs.
Always opt for custom installation and uncheck unfamiliar options, especially optional software that you never meant to download in the first place. Above all, avoid installing software that you don’t trust.
Seek help from the community for persistent problems
If problems persist despite your best efforts, don’t hesitate to seek help from the vast community of tech experts. They can provide valuable insights and practical solutions to resolve stubborn issues.
Cybersecurity threats rely on user ignorance, but knowledge is a powerful deterrent. So, continue familiarizing yourself with potential threats and security best practices.