How to Remove Bc20 from Mac (A Step-By-Step Guide)
Before we dive in
Before we dive in, let's make sure you stay safe online. We created SpyHunter because your security matters to us.
Protect your computer today — download SpyHunter right here! Check out our top tips below to keep your computer safe and secure.

Have you ever wondered about the resilience of your Mac’s security against the newest cyber threats, like the Bc20 malware?
This malicious software targets macOS devices specifically. It exploits system vulnerabilities and engages in deceptive practices, putting users’ privacy and digital safety at risk.
In this comprehensive article, we will explore the details of the Bc20 malware, including its common symptoms, how it infiltrates computers, and its impact on user privacy and security.
Understanding Bc20 malware
Bc20 malware has emerged as a significant threat targeting macOS devices, disrupting the seamless experience Mac users are accustomed to.
This malware exploits system vulnerabilities and user behaviors to navigate its way into the system, leaving users’ privacy and security at risk. Recognizing the impact of Bc20 is crucial for Mac users to take timely actions to safeguard their devices.
What exactly is Bc20 malware?
Bc20, a malicious software designed specifically for macOS, infiltrates Mac computers to steal sensitive information and create backdoors for hackers.
This includes usernames, passwords, and financial data. What makes Bc20 particularly dangerous is its ability to operate stealthily, collecting data without the user’s knowledge and potentially causing significant harm to the infected device.

Common symptoms of Bc20 infection in Mac computers
Identifying the symptoms of a Bc20 infection early can prevent severe damage. Common signs include a significant slowdown in computer performance, unexpected advertisements, and redirects to unwanted websites.
Users might also notice the installation of other unwanted applications, which suggests the presence of Bc20 adware. Such symptoms disrupt the device’s normal usage and hint at deeper issues within the system.
Why Bc20 malware is a threat to your privacy and security
Bc20 substantially threatens users’ privacy and security for several reasons. First, personal and financial information theft can lead to identity theft and financial fraud, impacting users beyond their digital lives.
Additionally, creating backdoors leaves the system vulnerable to further attacks, allowing hackers to access and control the compromised device remotely. This not only endangers the personal data stored on the device but also threatens the security of any network the device is connected to.
How does Bc20 malware sneak into Macs?
Bc20 malware intrusions into Mac devices are more intricate than one might assume. It exploits both system vulnerabilities and user behaviors. This particular form of malware adeptly finds its way through the digital cracks, making vigilance essential for Mac users.
The methods employed range from concealing itself within seemingly legitimate software bundles to deceptive advertisements masquerading as necessary updates. Understanding these tactics is the first step in fortifying your Mac against unwanted invasions.
Deceptive techniques used to distribute Bc20 malware
Deception is a vital tool in the Bc20 arsenal, with various strategies designed to trick users into unknowingly installing this malware.
One common approach involves using misleading prompts that appear on less reputable websites.
These prompts often imitate legitimate software update notifications, such as the frequently encountered Update Adobe Flash Player alerts. These fake alerts exploit the user’s trust and urgency to update their software, leading to the accidental installation of Bc20.
Furthermore, Bc20 can also be bundled with other applications, slipping into the system during installation, particularly when users opt for the default settings and neglect to scrutinize the bundled offers.
Could regular browsing habits put your Mac at risk?
Daily online activities could inadvertently expose Mac users to the risks associated with Bc20 malware. Downloading free software, clicking on pop-up advertisements, or browsing websites with questionable security can be gateways for Bc20 to infect your device.
These seemingly harmless actions can lead to significant security breaches, emphasizing the need for continuous caution and awareness while navigating the web.
The role of software bundles in spreading Bc20
Software bundling is a prevalent method through which Bc20 infiltrates Mac computers.
This approach entails packaging the unwanted program with other software, making it challenging for users to notice the malware’s addition.
Often, during the installation of legitimate applications, users may overlook the inclusion of Bc20 due to the pre-selected checkboxes or the opt-in conditions hidden within the Terms and Conditions.
Manually remove Bc20 malware from Mac
Discovering that your Mac is infected with Bc20 malware can be worrisome, but identifying the signs of infection is the first step towards reclaiming your system’s health.
This type of malware often manifests through unexpected advertisements, browser redirects, or unusual system performance issues. If you notice your Mac behaving oddly, it might be time to inspect it for malware.
Step 1: Identify and remove Bc20-associated files
To find any files related to Bc20, use the Finder utility to search through your Mac’s folders. Check these specific locations by using the Go and Go to Folder functions in the Finder window:
~/Library/Application Support/~/Library/Caches/~/Library/Preferences/~/Library/LaunchAgents//Library/LaunchDaemons//Library/LaunchAgents/
Look for files with “Bc20” in their names or those that appear suspicious. If unsure about a file’s purpose, an internet search can help determine its legitimacy.
Once located, drag these files to the Trash and empty the Trash to permanently delete them.
This ensures that Bc20-related files are completely removed from your system.
Step 2: Uninstall Bc20 from applications
Go to the Applications folder and scroll through the list of installed applications to find Bc20 or any unfamiliar, suspicious apps.
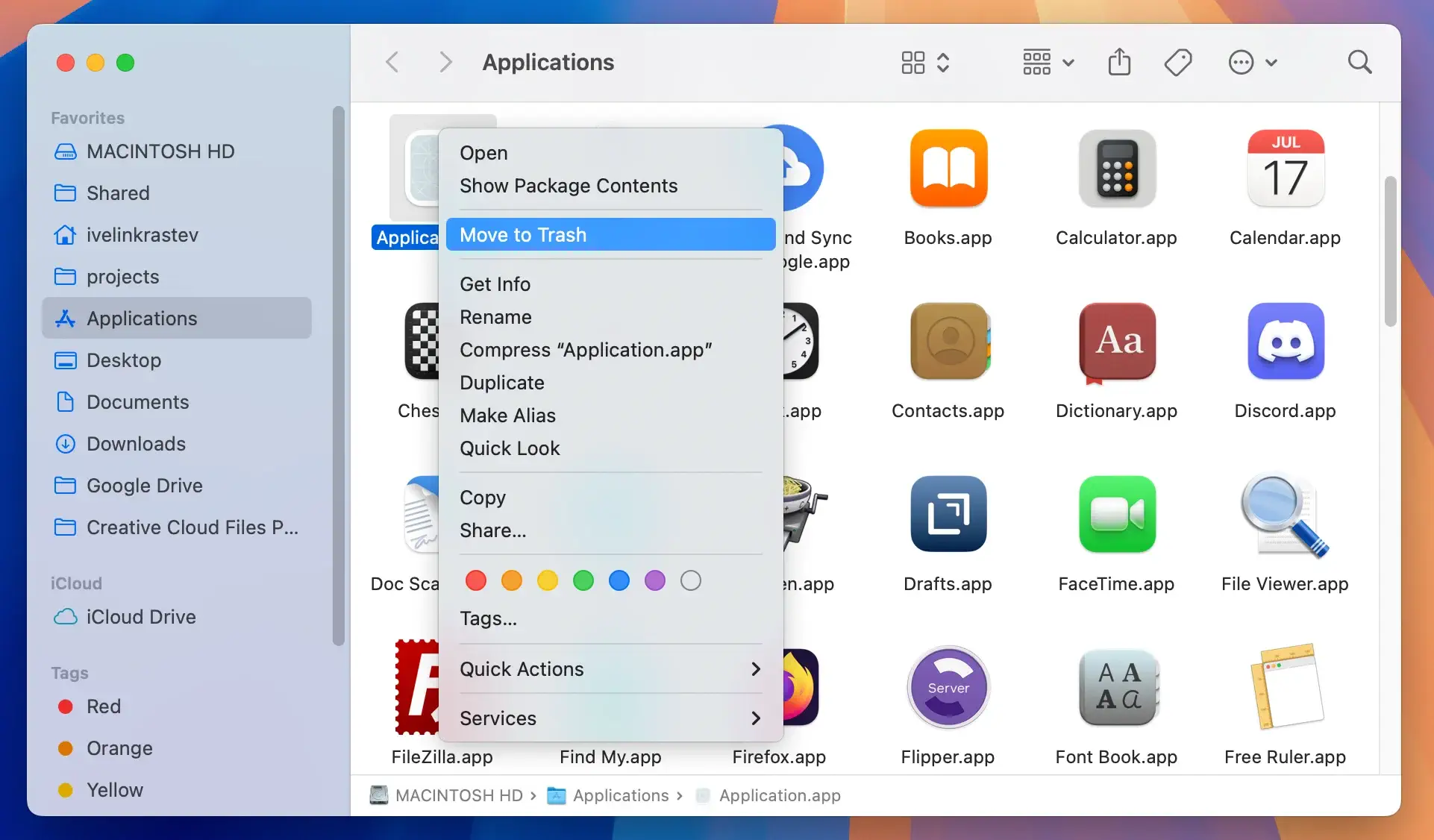
Right-click on the app, select Move to Trash from the context menu, and then empty the Trash to permanently remove the application.
Step 3: Eliminate Bc20 extensions from all browsers
How to remove Bc20 from Safari
Open Safari and navigate to the Preferences window under the Safari menu. Select the Extensions tab to view all installed extensions. Remove any extensions that you didn’t install or that look suspicious.
Deleting Bc20 extensions from Chrome
In Chrome, click the three dots at the top-right corner to access Settings, then select Extensions from the left-hand menu. Carefully review the list for unfamiliar extensions and click Remove to delete any that shouldn’t be there.
Purge Bc20 add-ons from Firefox
In Firefox, click the three bars to open the menu and select Add-ons. Go to the Extensions tab and examine the list for any unrecognized extensions. Click the three-dot icon beside the suspicious add-on and choose Remove to eliminate it.
Step 4: Remove profiles created by Bc20
Open System Settings and select Profiles under the Privacy and Security section. Look for any unusual or unidentified profiles and delete any related to Bc20 using the minus button.
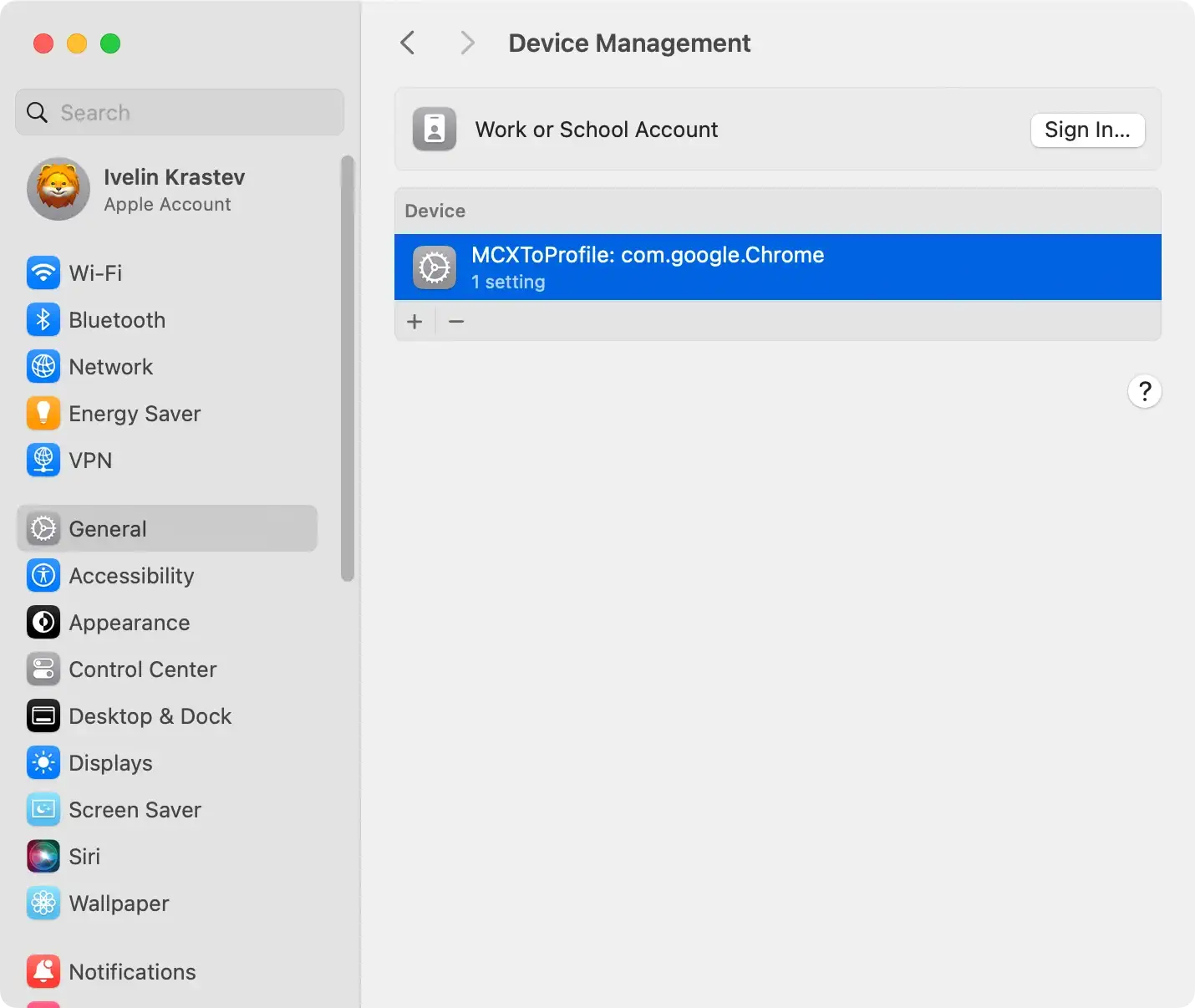
These profiles often contain settings that help the adware persist on your Mac.
Leveraging SpyHunter to eradicate Bc20 malware
Addressing malware threats like Bc20 on your Mac can seem daunting. However, with the right tools, it becomes manageable.
SpyHunter for Mac emerges as a powerful ally in this fight, offering comprehensive solutions tailored to remove Bc20 and other similar malware. Its efficiency lies in its sophisticated scanning algorithms that detect even the most elusive threats.
By opting for SpyHunter for Mac, you ensure your Mac’s security is in capable hands, safeguarding it against future infections.
Why choose SpyHunter for Mac for Bc20 malware removal?
Choosing SpyHunter for Mac for Bc20 malware removal offers several key advantages.
Its precision in identifying and eliminating malware components from your Mac ensures no traces of Bc20 remain. The tool is crafted to navigate the complexities of macOS, adapting to all versions for full compatibility.
Moreover, SpyHunter for Mac provides an added layer of protection by potentially optimizing your system’s performance, freeing up disk space previously occupied by malicious software.
Its user-friendly interface simplifies the process, making malware removal accessible to users with varying technical expertise.
With a free trial version, SpyHunter for Mac becomes attractive for those seeking comprehensive protection against digital threats.
How to use SpyHunter to detect and remove Bc20 effectively
- Download SpyHunter and install it. Installation is straightforward, ensuring that you can quickly move to the next step without hassle.
- Upon installation, launch SpyHunter for Mac and initiate a scan to detect the Bc20 malware on your Mac. The scanning process employs advanced algorithms to comprehensively identify any malware presence.
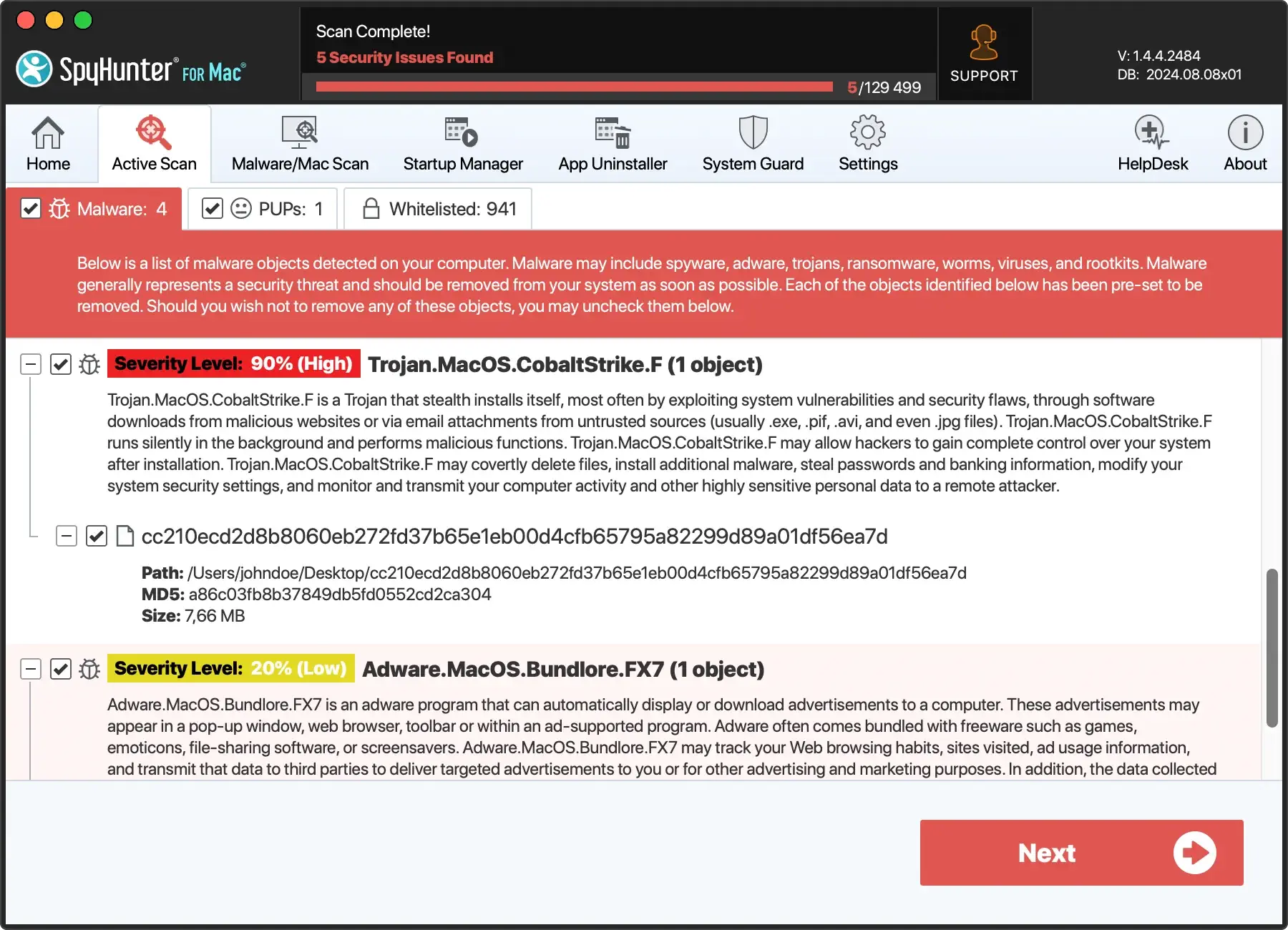
- After the scan, SpyHunter for Mac presents a detailed report of all detected threats, including Bc20 and other associated malware. Review the findings and remove the detected threats with just a click. This step not only eliminates Bc20 but also enhances your Mac’s overall security posture.
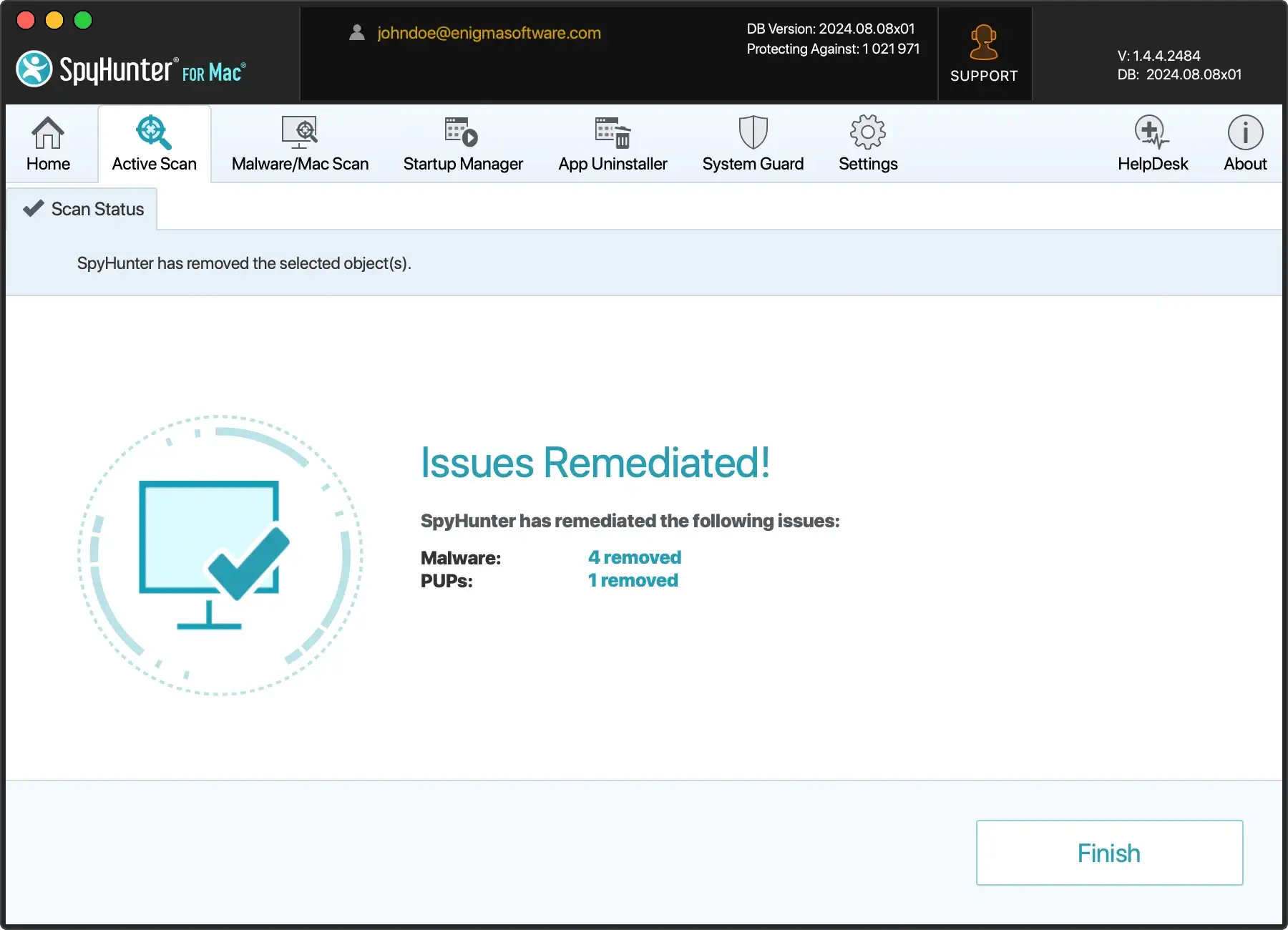
- With Bc20 effectively removed, SpyHunter for Mac offers tools to optimize your Mac’s performance. This process includes freeing up valuable disk space and making adjustments to improve system efficiency, ensuring your Mac runs smoothly post-cleanup.
Utilizing SpyHunter for Mac to address Bc20 malware provides a seamless solution that combines ease of use with potent malware removal and system optimization capabilities.
By following the simple steps outlined above, you can restore your Mac to its optimal state, free from the clutches of harmful software.
Restoring your Mac to its pre-infection state
After successfully removing malicious software from your Mac, restoring it to its original condition is a crucial next step.
This process involves several important actions to ensure your system runs smoothly and is free from any lingering security threats.
Carefully following these guidelines will help you recover your Mac’s optimal performance and safeguard your privacy.
Essential steps to clean and optimize your Mac post-removal
Once you’ve rid your Mac of harmful software, it’s time to focus on cleaning and optimizing your system to boost performance and prevent future infections. Here are key steps to consider:
- Update Your Software: Ensure all software, including the operating system and applications, are up to date. Software updates often include security patches that protect against malware.
- Review Your Applications: Remove any applications that are no longer needed or that you don’t recognize as legitimate. This reduces potential vulnerabilities in your system.
- Manage Startup Items: Some malware may add unnecessary programs to your startup list. Review and remove any undesired or unknown items from your Mac’s startup sequence to enhance boot times and system efficiency.
- Clean System Junk: Accumulated system and application cache can slow down your Mac. Use a reliable cleaning tool to remove unnecessary files and reclaim storage space.
- Perform Regular Scans: To detect and prevent future infections, regularly scan your Mac with a trusted anti-malware solution like SpyHunter for Mac.
Preventive measures against Bc20 malware
Defending your Mac against BC20 malware involves a proactive approach to cybersecurity. By understanding and implementing a series of straightforward preventive strategies, users can significantly diminish the risk of infection. The key lies in regular system maintenance, cautious online behavior, and reliable security solutions.
Safeguard your Mac from Bc20 and similar threats
Protecting your Mac from BC20 and similar malware starts with common-sense digital hygiene and is complemented by technical measures.
- Always ensure your macOS is up to date, as these updates often include crucial security patches.
- Be wary of email attachments or links from unknown sources, as these are common vectors for malware distribution.
- Limit downloads to trusted sites to avoid deceptive software that could harbor malicious code.
- Employ a reputable anti-malware tool to provide an essential layer of defense. Software like SpyHunter can detect and remove threats before they can cause harm.
Adjusting your Mac’s security settings for better protection
Adjusting your Mac’s built-in security settings can enhance your defense against malware like BC20. Enable the firewall in your system preferences to help block unauthorized incoming connections.
Consider activating FileVault to encrypt your hard drive, protecting your data even if your Mac falls into the wrong hands.
Also, familiarize yourself with the Privacy settings to control which apps can access your data, ensuring that only trusted applications can retrieve sensitive information.
Regular software updates: Your first line of defense
Software updates are crucial in protecting your Mac from malware and other security threats. Developers often release updates to address vulnerabilities that hackers could exploit to deploy malware like BC20.
Keeping your operating system and all applications up to date ensures that your device benefits from the latest security patches and performance improvements.
Although sometimes seen as a nuisance, regular updates are a fundamental aspect of digital security and should not be overlooked.
Conclusion
In wrapping up, it’s clear that addressing tech issues requires a straightforward yet careful approach.
Whether you’re dealing with common software errors or protecting your digital environment, the key is to use effective and user-friendly solutions.
For those who frequently encounter cybersecurity threats or system inefficiencies, SpyHunter offers a comprehensive and accessible remedy.
By prioritizing user experience and system safety, SpyHunter stands out as a preferred choice for individuals aiming to maintain a secure and optimally functioning digital space.