Complete Guide to Mac Adware [2025 Update]
Before we dive in
Before we dive in, let's make sure you stay safe online. We created SpyHunter because your security matters to us.
Protect your computer today — download SpyHunter right here! Check out our top tips below to keep your computer safe and secure.

Adware, also known as advertising-supported software, is software created to generate revenue for developers by automatically displaying online advertisements on your device.
Commonly appearing as pop-up windows or banners, these ads can disrupt your digital experience.
This article explains the mechanics of adware, offering insights on identification, impact, and removal strategies to safeguard your online environment. Let’s get down to business:
What is adware, and how does it operate?
Adware can be defined as a software component that, on the surface, may seem legitimate but is designed to intercept or record the user’s interaction with the system or to serve advertisements.
This form of potentially unwanted software presents users with online ads with the primary objective of generating revenue.
Adware can take root in your device in two ways. The first way occurs when adware is part of an app that the user knowingly downloads.
To monetize the application, developers integrate ads into the free version to motivate users to upgrade to a premium ad-free version.
However, adware does not always come packaged with genuine software. It can also install itself onto a device in a more malicious manner.

This form of adware often enters the system when an unsuspecting user accidentally clicks on an inappropriate link or when they download another piece of software.
The mechanisms of adware operation
Adware produces internet advertisements from the context of a user’s web browsers. Two main mechanisms support its operations.
Firstly, adware can operate as an independent program, entirely separate from other applications installed on a device.
The second form of operation is where adware presents itself as an integrated part of an online site or application. For instance, adware within a mobile application will display advertisements while the user is using this app.
The revenue then accrues from ad impressions or user clicks on the ads.
How adware is unknowingly installed
Adware installations occur unknowingly when users accidentally click on a suspicious link or download infected software. A typical scenario is when adware is bundled up with free software downloaded online.
During installation, the unsuspecting user unknowingly lodges the adware alongside the legitimate software. Notably, even personalized ads may not be safe.
Some adware collects data about a user’s browsing habits and sells it to third parties, allowing for more tailor-made and potentially harmful advertisements.

Adware as a potentially unwanted program (PUP)
To understand the full scope of adware, it’s essential to discuss its classification as a Potentially Unwanted Program or PUP. This term commonly applies to programs bordering on being harmful and intrusive, such as adware.
The specifics of adware as a PUP, other types of PUP, and the legal issues regarding these programs are explored below.
Classification of adware as a PUP
Adware is classified as a Potentially Unwanted Program (PUP) due to its invasive and often unwanted presence on a user’s device.
The primary function of adware is to generate revenue by displaying intrusive online advertisements, often without the user’s full knowledge or consent.
Although some adware may be part of a legitimately downloaded app, much of it is installed unknowingly and unwelcomely.
Other types of PUPs
Beyond adware, there are several other categories of Potentially Unwanted Programs.
Examples include spyware, which covertly obtains information on a user’s activities; browser lockers that restrict user access to their browser; dialers that can make unauthorized calls or connections; and junkware, which clutters your system with unnecessary files and applications.
Browser hijackers are another type of PUP. They quietly infiltrate browsers such as Safari or Google Chrome and modify their settings. Modifications include changing the default homepage and search engine, adding buttons to the menu bar, causing browser redirects, and accessing browsing history.
Browser hijackers are often distributed in the form of unwanted extensions for your browser, commonly found on misleading websites.
Browser hijackers are commonly distributed through malicious websites that can quietly install the PUP without the user’s knowledge or explicit consent.
The legal issues surrounding PUPs
The subtle nature of PUP installation creates a tricky legal landscape.
Since users technically agree to install these programs, often unknowingly during the installation of other software, security companies have straddled the boundary between categorizing them as minor nuisances or significant security threats.
While a sensible user would not want these programs on their computer, any steps taken by security companies to block them outright as malware can lead to potential legal issues, making the fight against adware and other PUPs a delicate matter.
Despite these challenges, the cybersecurity industry continues to progress in legal battles and public opinion against software providers whose programs are considered more than just slightly bothersome.
Ultimately, user protection is prioritized.
How does Adware infect your device?
Understanding the modes of adware infection is crucial to preventing unwanted ad intrusions on your devices.
In this part, we will explore the common pathways for adware infection, the deceptive strategies of adware creators, and how adware affects different platforms.
Common ways for a computer to get infected by Adware
Adware typically infiltrates a system through software vulnerabilities, bundled software, or unintentional downloads through pop-up banners. Hackers can exploit security weaknesses in your software or OS and insert adware into your system.
Cybercriminals often launch clandestine adware attacks through ‘drive-by-downloads,’ which exploit browser vulnerabilities and quietly load malicious codes when an unwitting user unintentionally visits a malicious website.
In addition, software bundling is a standard method used by adware developers. In this case, the adware hides within a legitimate, freely downloadable app. Users, therefore, inadvertently install the adware app while procuring the primary application.
Other typical methods of adware infections involve downloadable toolbars, browser extensions, or files from suspicious websites, torrents, or piracy sites.
The deceptive techniques used by adware makers
Adware creators often use ingenious yet deceptive techniques to mislead users into downloading their unwanted software.
For instance, adware can be made to appear helpful, masking itself as a genuine tool—for example, a video player or a browser plugin. However, on closer inspection, this purported utility program is simply an adware installer.
In other instances, adware makers employ misleading methods like graying out or minimizing options to decline their offer, pre-checking boxes on installation windows, or heavily promoting a ‘preferred’ option.
Such deceptions can lead to unwanted adware downloads and installations.
How do you remove adware infections?
Responding efficiently and effectively to adware on your Mac can minimize damage and ensure a more secure device in the future.
This section discusses the critical initial steps to handle potential adware infection, tools available for removal, difficulties in tackling aggressive adware forms, and prevention methods against possible adware attacks.
Initial steps to take against Adware
When facing a potential adware infection, it is paramount to determine if your software or operating system has indeed been compromised.
This process involves monitoring for an unusual flurry of pop-ups and ads, unexpected browser settings changes, unfamiliar toolbars or browser extensions, and a noticeable downfall in system performance.
If these signs are present, it could indicate an adware infection.
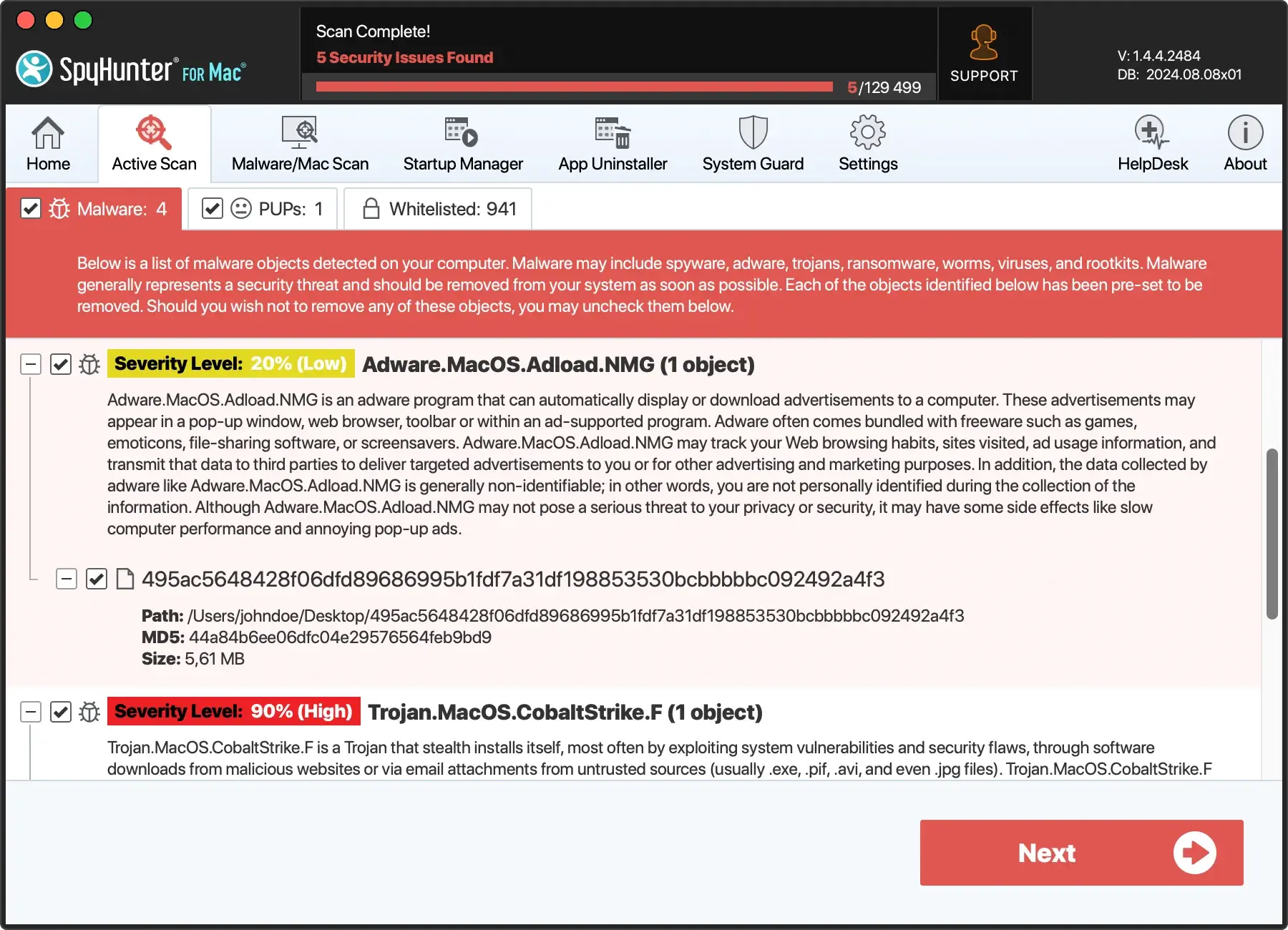
Use an adware removal tool
To get rid of adware, you might have to employ adware removal tools to eradicate adware from your system.
Many reliable security solutions, such as SpyHunter for Mac, are designed for this purpose. SpyHunter can scan your system, identify adware or other malicious programs, and safely remove them.
However, it’s worth noting that these solutions work best when used with continually updated malicious files definitions since adware creators frequently modify their malicious software to avoid detection.
Download SpyHunter and complete the installation. Then, you can run a scan of your system for any potential adware that may be lurking on it.
Removing more aggressive adware forms
Some forms of adware apps are more aggressive and difficult to remove than others. Adware makers have devised techniques to circumvent modern ad-blocking tools, including defense tools, preventing adware removal.
These tools block security software from running or even being installed and stop users from executing measures to remove the adware.
They represent a significant shift in the tactics of adware developers from merely annoying to downright malicious.
Prevention methods against adware attacks
Since some adware types are incredibly resilient and challenging to eliminate, prevention is the best strategy against adware attacks. Here are a few steps to take toward this effect:
- Be vigilant of what you download and click on, especially with freeware and enticing offers.
- Update your software regularly to eliminate the risk of security holes.
- Install a safe, reliable security solution with adware and malware-blocking features like SpyHunter for Mac.
These measures can help deter adware from infiltrating your system in the first place, keeping your device safer and more secure.