How To Remove ConnectionOptimizer (Mac)
Before we dive in
Before we dive in, let's make sure you stay safe online. We created SpyHunter because your security matters to us.
Protect your computer today — download SpyHunter right here! Check out our top tips below to keep your computer safe and secure.

ConnectionOptimizer is a malicious application classified as adware. Predominantly targeting the Mac platform, this intrusive program functions by seizing control of your browser homepage and default search engine, redirecting your searches through ConnectionOptimizer Search.
This comprehensive guide will explore helpful techniques to help you remove ConnectionOptimizer from your Mac.
What is ConnectionOptimizer?
One might wonder, what is ConnectionOptimizer? Essentially, it is a pernicious adware application designed to generate a stream of unwanted advertisements.
Beyond this, ConnectionOptimizer also tracks online data from the devices it infiltrates.
Potentially armed with spyware and keyloggers, it can do more harm to your Mac computer and possibly even compromise confidentiality by invading your personal information.
Common symptoms of ConnectionOptimizer infection
Several prevailing symptoms designate the presence of the ConnectionOptimizer browser hijacker.
- The victim’s web browser default search engine changes to ConnectionOptimizer Search.
- Browser search queries are redirected through ConnectionOptimizer Search, leading to unfamiliar search results.
- The “ConnectionOptimizer” browser extension or program is installed on the affected Mac.
The adware also presents a monumental issue with displaying countless unwanted ads in varying forms, such as push notifications, pop-up windows, promotions, coupons, and even fake alerts.
These intrusive adverts not only disrupt the web browsing experience but can also significantly compromise the computer’s performance, security, and user privacy.
How was ConnectionOptimizer installed on my Mac?
Installing malicious programs such as ConnectionOptimizer often occurs covertly and sometimes even with the user’s unknowing assistance.
The question often raised by affected users is, how did they end up with unwanted software on their Mac? Most of the time, the infiltration of such hazardous environments into a computer system occurs through muses of techniques cyber criminals employ to dupe unsuspecting users.
Unintentional user installation
One standard method for installing ConnectionOptimizer is vigorous advertisements or camouflage under reputable applications. Users are often left baffled about the origin of such software, as they do not recall intentionally downloading or installing it.
In some regrettable cases, Mac users may intentionally install ConnectionOptimizer due to deceptive programming and marketing techniques that paint the software as beneficial without being aware of its adverse side effects.
In either case, the result is the same – an unwanted program installed on the user’s Mac without their consent or awareness.
Bundled with other software
Another typical method for the infiltration of ConnectionOptimizer into a user’s Mac is through a technique called software bundling.
This involves coupling the adware application with other seemingly harmless programs in a single executable setup file. When the user downloads and installs these programs, ConnectionOptimizer gets installed.
At times, the adware program may be advertised as a beneficial add-on or a bonus software, successfully tricking users into installing it for perceived benefits.
Additionally, specific free downloads fail to explicitly divulge the installation of additional software, such as ConnectionOptimizer, leading to inadvertent consent on the user’s part. In some cases, ConnectionOptimizer may even be distributed through a fake software update, hence sneaking onto the computer undetected.
How to remove ConnectionOptimizer?
Faced with a ConnectionOptimizer intrusion, removing the rogue application swiftly is integral to prevent further harm to your Mac and loss of personal information.
To achieve this, follow the outlined sequence of steps to ensure the comprehensive removal of ConnectionOptimizer from your computer, where we discuss profiles, app removal, file deletion, and scanning with SpyHunter.
Delete malicious configuration profiles
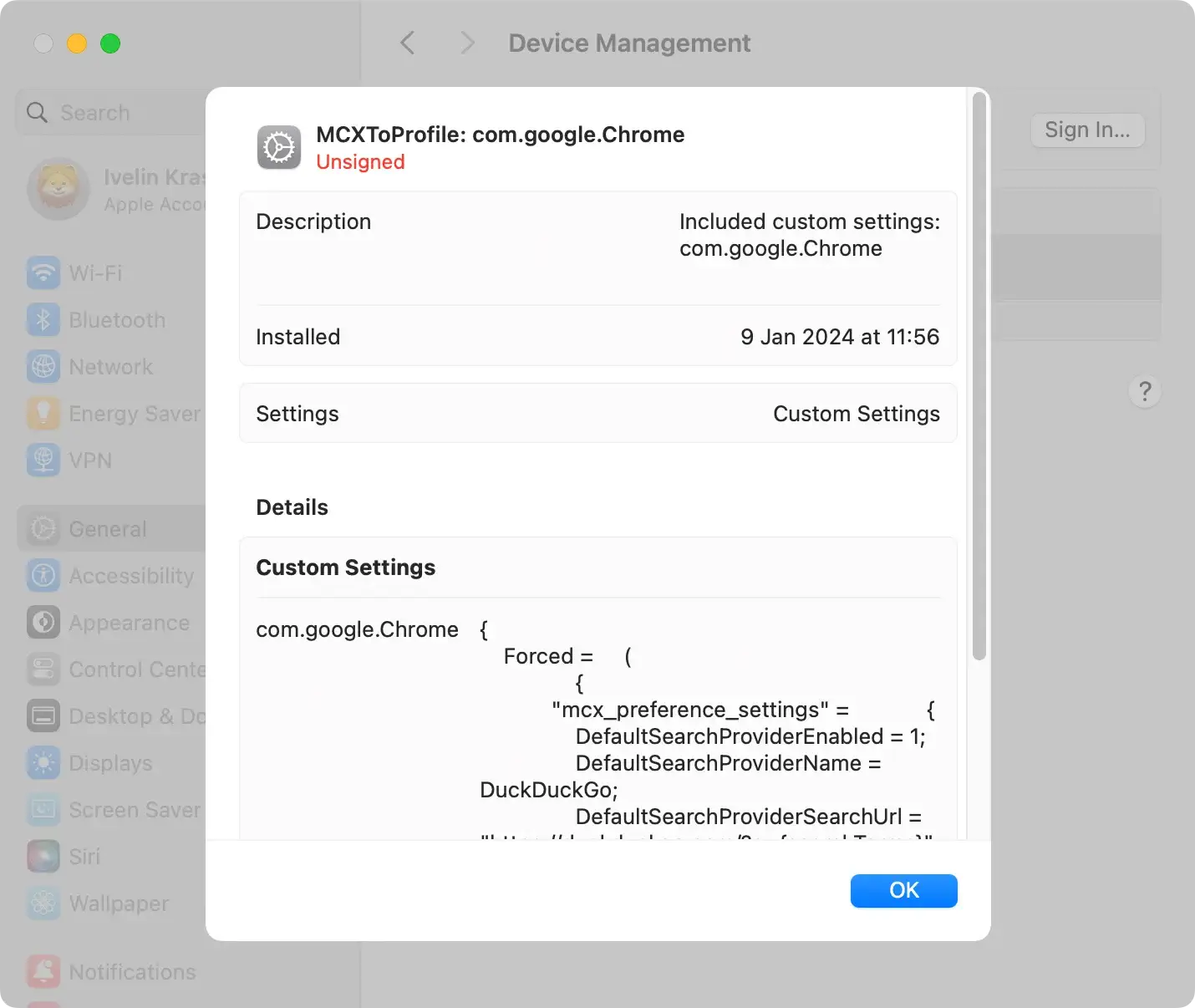
The first step involves eliminating any profiles that ConnectionOptimizer may have created on your Mac.
Often, adware programs generate a profile to grant themselves permissions or set specific settings that make their operation more manageable. Hence, these profiles need to be removed promptly.
Follow these steps to identify and delete them:
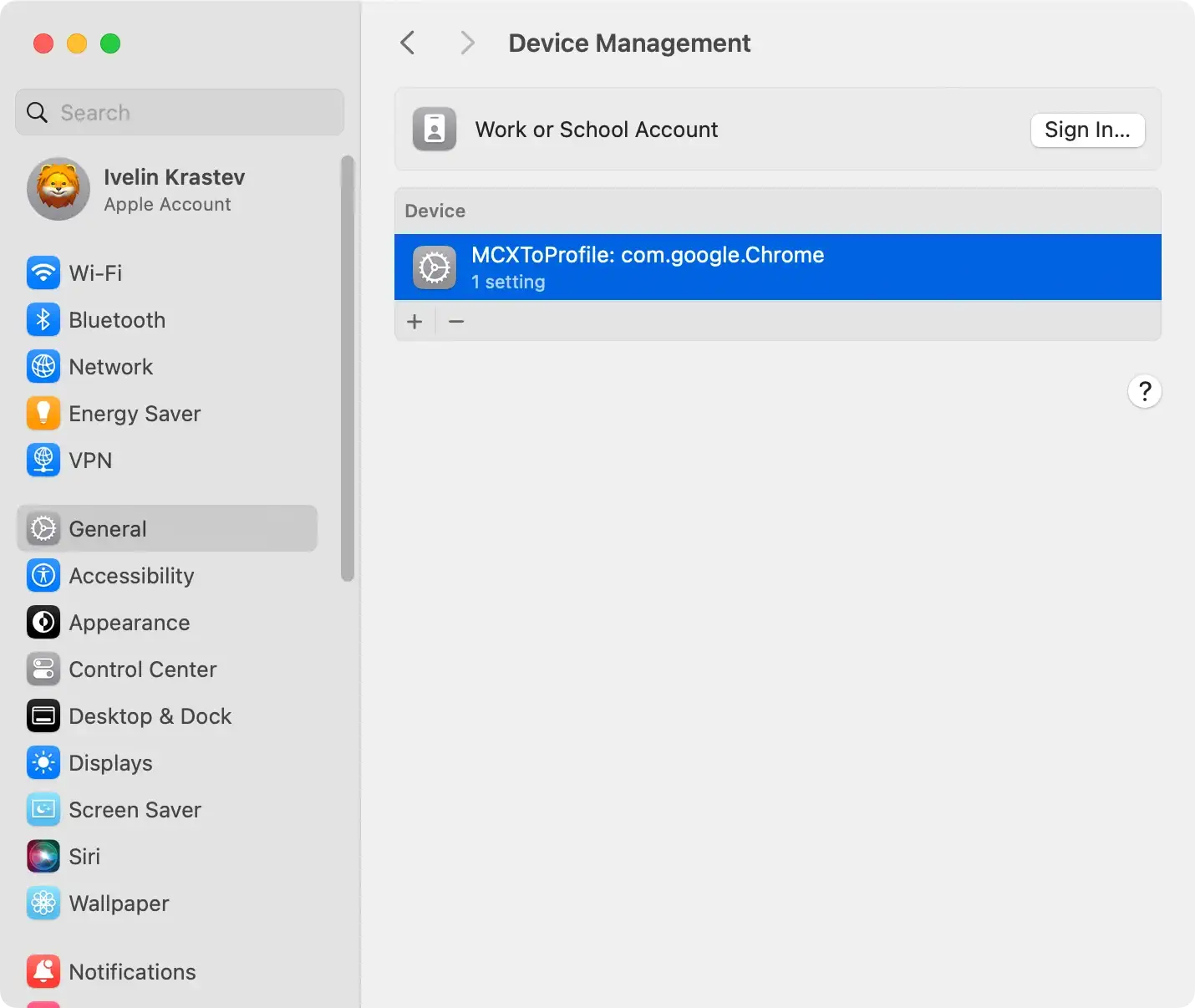
- Open
System Settingsand locate theProfilessection underPrivacy & Security - Review the profiles and identify any suspicious ones you wish to remove
- Click the ‘-‘ (minus) button and confirm the removal
Remove ConnectionOptimizer from Applications
Next, you must clear out any potentially harmful apps associated with ConnectionOptimizer that might exist on your Mac.
To do this, navigate to the Applications folder and find and delete any suspicious applications. Be mindful, however, that some malicious programs use innocent-looking names or mimic the name of reputable software to avoid being detected.
Therefore, research any unknown applications before you decide to keep them.
Tip
Consider using SpyHunter for a more comprehensive approach to app removal. It is a powerful anti-malware program that includes a high-tech app uninstaller.
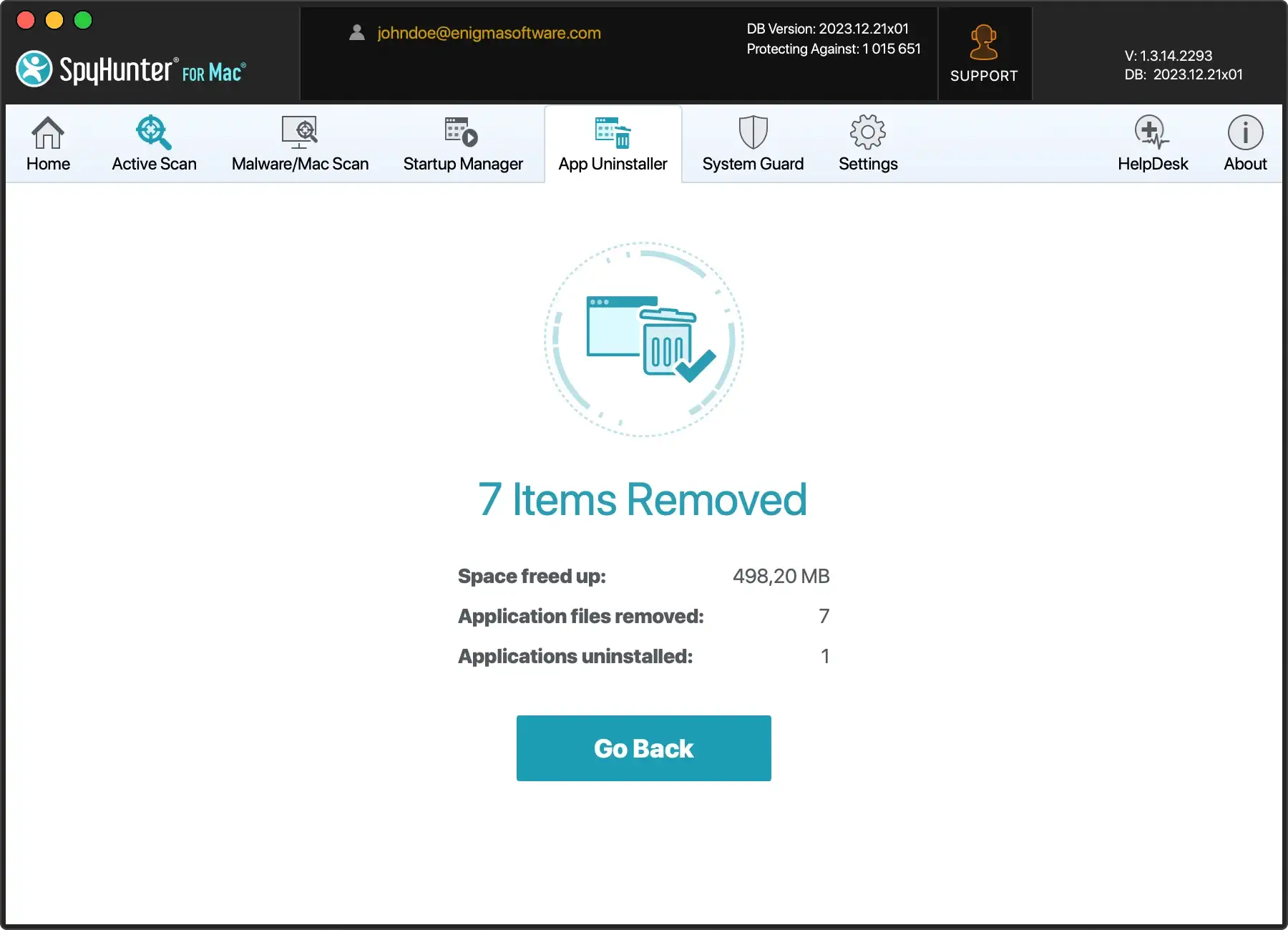
Follow these simple steps:
- Download SpyHunter for free here and follow the installation instructions.
- Click on the App Uninstaller tab. This will initiate an automatic application scan.
- Select the applications you want to remove and click the Remove button.
Run a scan for malicious software
After manually removing malicious profiles and related apps, scanning your Mac with credible anti-malware software such as SpyHunter for Mac is highly recommended.
This step can be instrumental in uncovering and removing any lingering traces of ConnectionOptimizer. SpyHunter offers comprehensive protection against malware, adware, and browser hijackers like ConnectionOptimizer.
It identifies and eliminates such threats, purging your Mac system and providing peace of mind.
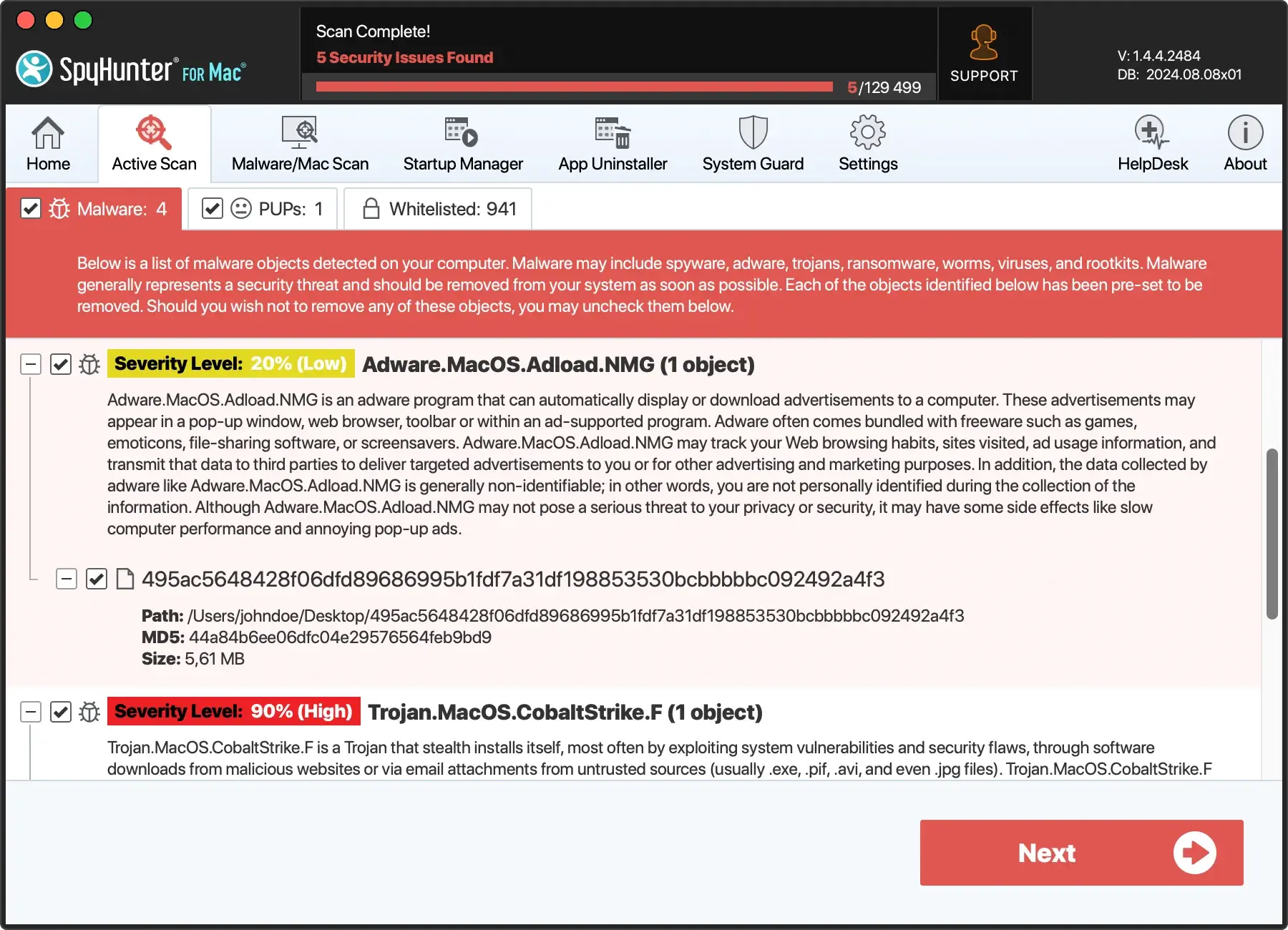
The subsequent step involves removing any files and folders related to ConnectionOptimizer from your computer.
This clearance step ensures that no residual files from the malicious application are left lurking in your system’s directories.
Remove ConnectionOptimizer from your browser
Last but not least, it’s time to focus on the area where ConnectionOptimizer is most active – your internet browsers.
This unwanted utility is not only a stand-alone program; it also integrates with your web browsers as an extension, seizing control over your online activities.
Therefore, eliminating it from browsers such as Safari, Chrome, and Firefox is critical in regaining control over your web browsing experience.
Tips for Safari
For Safari, start by selecting Preferences from the Safari menu. This will open a new window where you can click the Extensions icon to view all installed extensions.
Try to identify any extensions that belong to ConnectionOptimizer or appear to be suspiciously related. Upon identification, proceed to remove these unwelcome extensions. Remember that the unwanted program frequently uses deceptive names or mimics the names of legitimate extensions.
Hence, make sure to examine each extension that you don’t remember installing.
Tips for Chrome
If Google Chrome is your primary browser, begin the removal process by selecting Preferences from the Chrome menu.
Next, click the Extensions link on the left-hand pane to open a list of installed extensions.
Like in Safari, you’ll need to find and remove any extensions that belong to or seem related to ConnectionOptimizer. Remember, the adware cleverly masks itself to blend in, so don’t hesitate to research unfamiliar extensions and remove anything that doesn’t seem right.
Tips for Firefox
If you are a Firefox user, the process differs slightly. Select Add-ons from the Firefox menu to open a new window with a list of installed extensions and plugins.
You would need to look into the Extensions and Plug-ins lists to detect any traces of ConnectionOptimizer. Once identified, hit Remove or Uninstall to discard the harmful extension.
Remember that it is necessary to leave no stone unturned; any active extension or plugin that belongs to or is associated with ConnectionOptimizer must go.
Once you have cleaned out the rogue extensions from your browser, close and reopen the browser for the changes to take effect.
This thorough cleansing of your web browsers helps ensure a safer and cleaner browsing experience, free from intrusive ads and constant redirects.
How to stay safe on the internet?
In an era where our lives are increasingly intertwined with the digital realm, ensuring our safety on the internet has never been more crucial.
From personal communication to financial transactions, the Internet offers unparalleled convenience but presents potential risks. Cyber threats, scams, and privacy concerns are ever-present challenges.
However, you can navigate the online landscape securely with the proper knowledge and habits.
Whether you’re a seasoned cybercitizen or just starting your online journey, these guidelines will empower you to protect your digital presence and enjoy the vast benefits of the internet with confidence.
Use reliable antivirus software
Begin by equipping your device with trusted antivirus and anti-malware software. Programs like SpyHunter for Mac offer real-time protection against online threats. They provide a strong defense against malicious software.
Enable two-factor authentication (2FA)
Activate 2FA whenever possible. This adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
Use strong passwords
Create unique and strong passwords for your online accounts. Include a mix of uppercase and lowercase letters, numbers, and symbols. Avoid using easily guessable information, such as birthdays or names.
Be skeptical of emails and messages
Be cautious when clicking links or opening attachments in emails or messages, especially if they are unexpected or from unknown sources. Phishing attempts often use these methods to trick users into revealing sensitive information.
Keep your software up-to-date
Regularly update your operating system, antivirus software, and other applications. Updates often include security patches that help protect your devices from vulnerabilities.