What Is Gatekeeper And How To Use It [Guide For Mac Users]
Before we dive in
Before we dive in, let's make sure you stay safe online. We created SpyHunter because your security matters to us.
Protect your computer today — download SpyHunter right here! Check out our top tips below to keep your computer safe and secure.

Gatekeeper on macOS is a vigilant guardian of your system’s security. It is meticulously designed to ensure only trusted software runs on your device.
This integral feature of macOS is the first line of defense against malware and unauthorized applications.
Gatekeeper verifies the developer’s identity and ensures the software hasn’t been tampered with since its release.
In this article, we’ll explore the workings of Gatekeeper, its role in maintaining your Mac’s security, and how you can customize its settings.
Whether you’re a long-time Mac user or new to the ecosystem, understanding Gatekeeper is critical to ensuring a secure and smooth computing experience. Let’s dive in:
Introduction to Gatekeeper on Mac
In the quest for digital safety, macOS has taken significant strides in creating Gatekeeper, a cornerstone security feature that embodies Apple’s commitment to user privacy and data protection.
This introduction explains Gatekeeper’s functional essence and operational mechanics, paving the way for a deeper understanding of its crucial role in the macOS ecosystem.
What is Gatekeeper on Mac?
Gatekeeper is an integral component of macOS, serving as a vigilant security checkpoint for software authorization.
Its primary role is safeguarding macOS users from harmful applications by ensuring that any software installed on their Mac has been vetted for safety.
Gatekeeper achieves this by verifying that an application is not only from an identified developer but also notarized by Apple, indicating it has been checked for malicious content and approved for use.

Whenever a user attempts to open an app downloaded from outside the Mac App Store, Gatekeeper intervenes. It conducts a rigorous authenticity and safety check before running the app.
This system is designed to protect you from inadvertently installing malware or other malicious software, maintaining the integrity of your devices and personal data.
Why do you need macOS Gatekeeper?
The internet is a vast expanse of resources, but it also harbors potential threats that can compromise user safety and data integrity. Files downloaded from places outside of the App Store may hide threats.
The Mac operating system, like other operating systems, is susceptible to these threats, which can be present in the disguise of software applications.
Gatekeeper is a critical line of defense in Apple’s comprehensive security strategy, providing an automated screening process that significantly reduces the risk of installing harmful software.
Through developer identification and notarization mechanisms, Gatekeeper ensures that only trusted software can run on a user’s Mac, protecting the user from malware, data breaches, and other cyber threats.
With the increasingly sophisticated nature of online threats, the role of Gatekeeper in preserving both the functionality and security of macOS devices is more critical than ever.
It represents Apple’s proactive approach to cybersecurity, balancing operational freedom with maintaining a safe computing environment for all users.
How does Gatekeeper enhance security?
The macOS operating system is renowned for its robust security features, among which Gatekeeper is pivotal.
Gatekeeper enhances the protection of macOS in several ways, offering a multi-layered defense strategy against the infiltration of malicious software.
By controlling access to macOS through strict verification processes, Gatekeeper ensures that only secure, Apple-approved applications can operate on the user’s system.
The role of Gatekeeper in macOS protection
Gatekeeper’s primary function is to ensure that the software you download and install on your Mac is safe and trustworthy.
It does this by enforcing strict verification standards that all applications must pass before they can be opened. Mac App Store apps are inherently trusted, having gone through Apple’s extensive review process.
However, for software obtained from outside the Mac App Store, Gatekeeper verifies the developers’ identity and confirms that Apple notarizes the application. This is a process known as code signing.
A downloaded file with a code signature is flagged as safe by the Gatekeeper check, even when downloaded from a source outside the App Store.
This notarization process involves a detailed check to ensure the application is free from known malware and exploits. By setting these barriers, Gatekeeper significantly mitigates the risk of malicious software penetration, safeguarding your Mac from potentially harmful content.
The mechanism behind Gatekeeper’s operation
Gatekeeper works through a series of checks and balances that are seamlessly integrated into the macOS framework.
When an application is downloaded from the Internet, Apple assigns it a particular attribute indicating that the file is under quarantine.
Upon attempting to open the application flagged with a quarantine attribute, Gatekeeper takes over, examining the source of the file and its certification status.
This mechanism extends to protect app users against cleverly disguised malware, such as applications masquerading as innocent files or those that may attempt to load malicious plugins.
Furthermore, Gatekeeper can confine apps to operate from randomized, read-only locations, which thwarts the unauthorized loading of external plugins.
One of Gatekeeper’s fundamental alerts is the block message "App Name" will damage your computer.
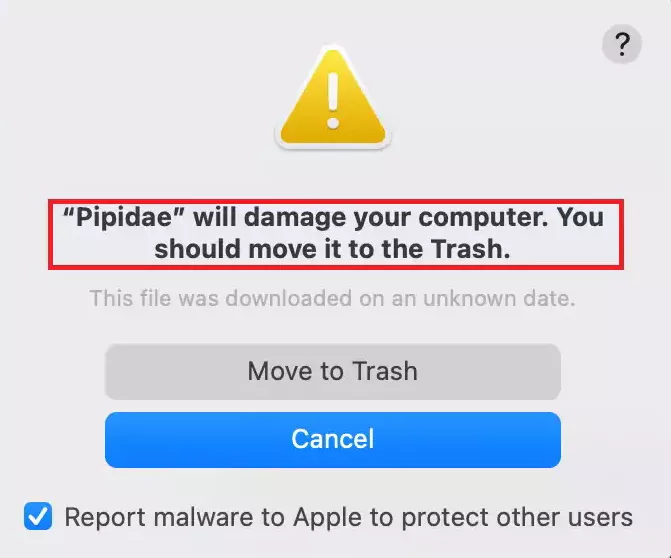
This warning is crucial in informing users about potential risks, indicating that the app they’re attempting to open has been flagged as malicious or untrustworthy.
Gatekeeper’s limitations: How to enhance protection
Gatekeeper, a pivotal security feature in macOS, is designed to protect users by ensuring that only apps from the App Store or identified developers can be installed.
This mechanism, which includes file quarantine and security settings, aims to keep your computer safe from malware and other security risks.
However, Gatekeeper has vulnerabilities, such as the potential for Gatekeeper bypasses, which savvy cybercriminals can exploit.
While Gatekeeper relies on developer certificates to verify the legitimacy of apps downloaded, this system can be circumvented.
For instance, if malware disguises itself within installer packages or app bundles from seemingly legitimate applications, it might not trigger Gatekeeper warnings.
Moreover, macOS Gatekeeper focuses on the initial installation process. It doesn’t offer real-time protection against malware that might exploit vulnerabilities post-installation, such as those that could bypass system integrity protection or modify system preferences without user consent.
Enhancing protection with SpyHunter for Mac
SpyHunter for Mac emerges as a robust solution to address these concerns and offer a layer of security beyond what Gatekeeper provides.
SpyHunter enhances your Mac’s defenses with real-time scanning capabilities, identifying and removing known malicious content and monitoring for suspicious behavior indicative of malware that could evade Gatekeeper’s checks.
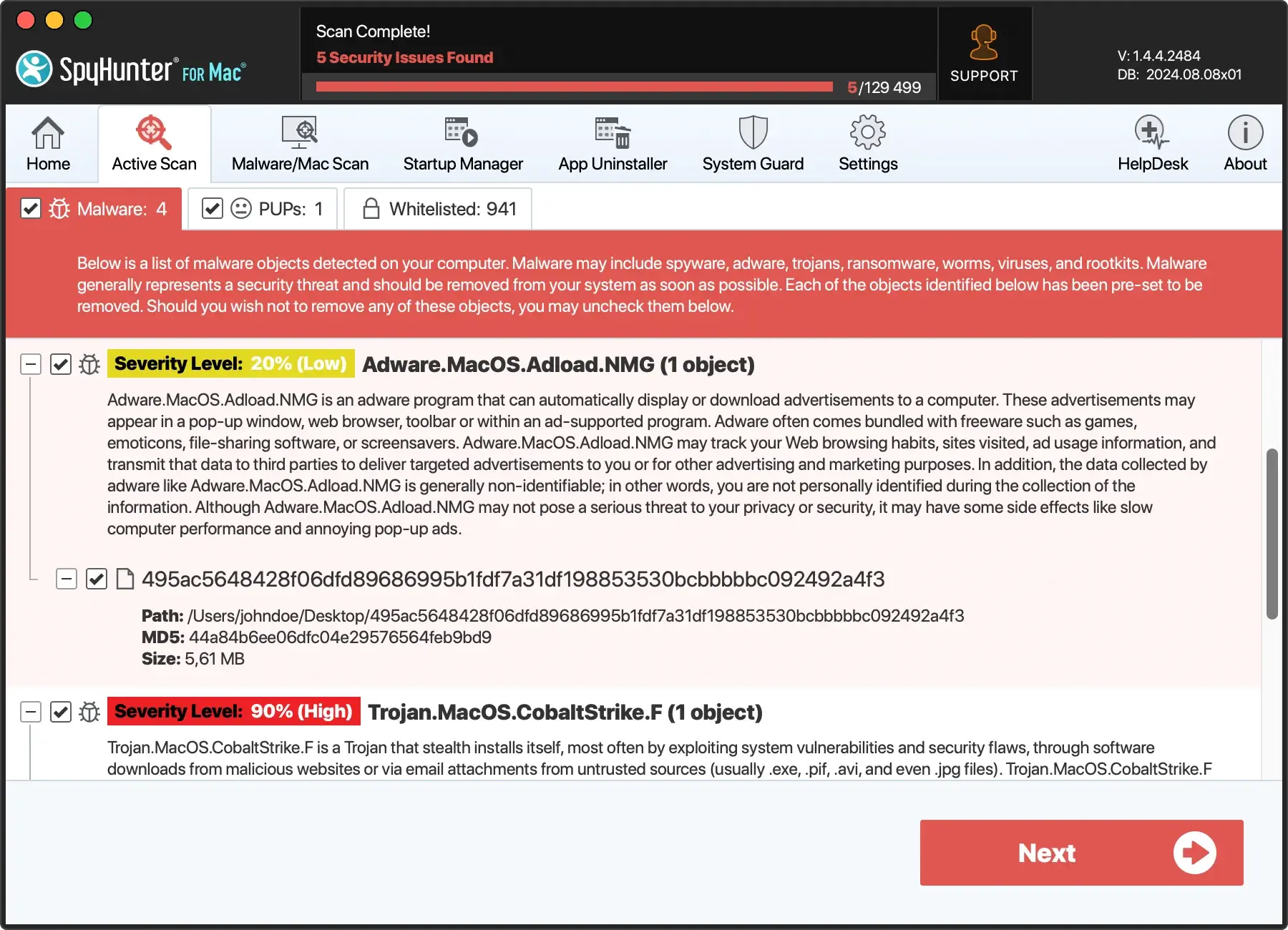
It’s particularly effective against sophisticated threats that exploit the quarantine extended attribute or manipulate downloaded files to gain access to your system.
SpyHunter for Mac also complements Gatekeeper’s efforts to enforce security policies by offering additional protection layers, including:
- SpyHunter monitors applications downloaded from the internet, ensuring they’re safe and malware-free.
- It also scans downloaded disk images and new app bundles, checking for extended attributes that might suggest a security risk, thus ensuring your data remains protected.
Download SpyHunter and integrate it with Gatekeeper’s security measures. This will ensure a comprehensive defense strategy, enhancing the security settings of your macOS.
Whether you’re running macOS Mojave or a newer version, this combination of security solutions keeps your access to apps secure, maintains system integrity, and protects end users from the latest cyber threats.
Navigating Gatekeeper settings for optimal security
Understanding and navigating Gatekeeper settings is crucial for macOS users looking to maximize their protection and level of user control over their system.
These settings are the foundational controls for managing which applications can be installed and run on your Mac, thus playing a pivotal role in your device’s overall security posture.
Adjusting your Gatekeeper settings
To access your Gatekeeper settings, navigate to System Preferences (named System Settings on newer macOS versions), specifically the Security & Privacy section.
Locate the options that control the sources of applications your Mac can run. The available settings let you choose between allowing apps downloaded from the App Store only or both the App Store and identified developers.
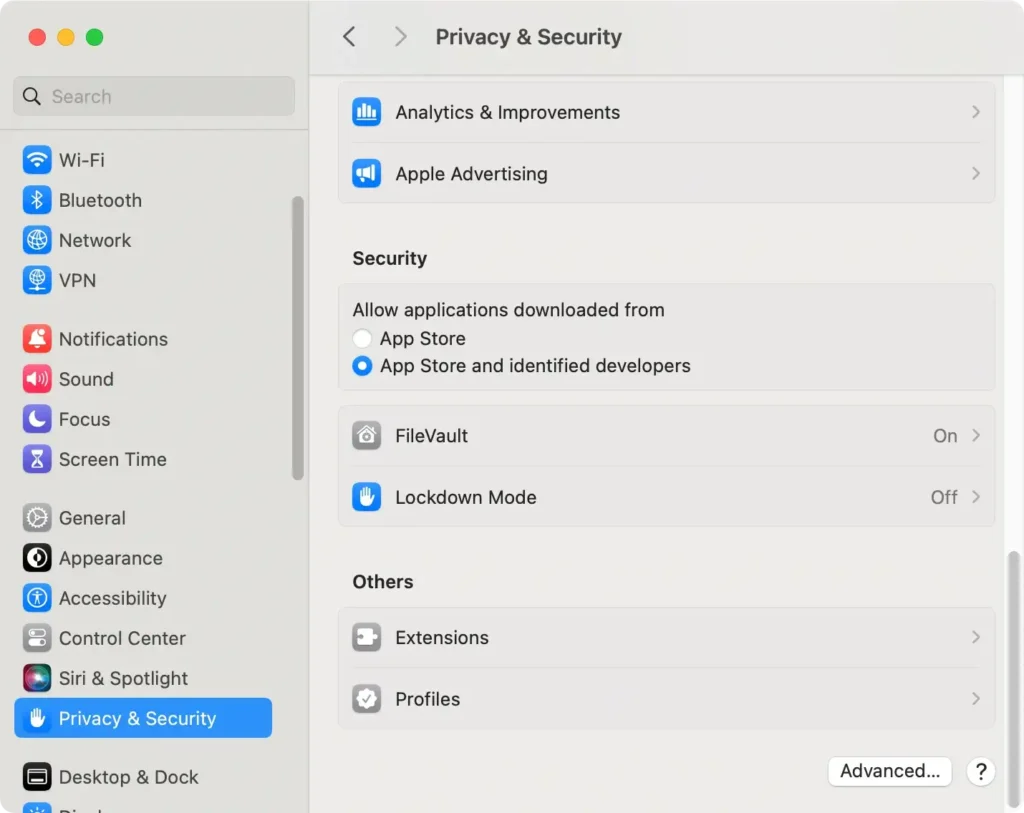
It’s important to note that changing these settings requires authentication, so you must authenticate with your admin password.
Common Gatekeeper configuration scenarios
- For Enhanced Security: Users seeking to minimize their exposure to potentially harmful apps can choose the most restrictive option, allowing only apps from the App Store. This setting is handy when the Mac is used by people who might not know how to assess the safety of third-party apps. This includes children or individuals with limited tech experience.
- For Developer or Power User Needs: People who install software from different sources might prefer the “App Store and identified developers” setting. It’s a good compromise. This option lets users install more software types. At the same time, it keeps things secure. Apps must be approved by Apple or made by developers Apple recognizes.
- Temporary Adjustments for Specific Installations: Sometimes, Gatekeeper might not recognize a trusted app. When this happens, you might need to change your settings. You can adjust your settings or right-click the app and select “open” to bypass Gatekeeper once. After installing the app, switching back to stricter settings is wise.
Understanding Gatekeeper settings is fundamental for maintaining optimal security on your Mac.
The settings offered and their possible changes can meet many needs. But always be careful. Make informed choices about balancing convenience and security.
Overriding Gatekeeper: When and How
Despite Gatekeeper’s role in safeguarding macOS from malicious software, there are instances when a legitimate app might be blocked due to its stringent protocols.
Gatekeeper bypass methods
Gatekeeper bypasses should be approached with caution and only when necessary. Mac OS provides two primary methods to bypass Gatekeeper for applications that a user trusts but are not yet notarized or recognized by Apple:
- Manual Overrides per Application: A manual override can be performed by attempting to open the app while holding down the Control key. This action triggers a dialog box that allows opening the app regardless of its unrecognized status. This method requires the user to acknowledge the risk, thereby making a deliberate decision to trust the software.
- Changing Gatekeeper’s Settings: You can modify Gatekeeper’s settings via the Security & Privacy panel in System Preferences for a broader approach. This allows temporary adjustments to Gatekeeper’s operational mode, enabling software installation from less restrictive sources. However, this method exposes the system to a broader range of potential threats and is recommended only for those who understand the security implications.
- Utilizing the ‘spctl’ Command: Administrators may use the ‘spctl’ command in Terminal to manage Gatekeeper’s app blocking on a granular level. This method allows you to disable Gatekeeper for individual apps. However, familiarity with command-line operations is a prerequisite.
These methods provide flexibility in-app security, including disabling Gatekeeper, while carefully assessing and accepting the associated risks.
Tips for securely managing exceptions
While legitimate reasons exist to bypass Gatekeeper, managing exceptions securely to mitigate potential vulnerabilities is crucial. Here are some tips for doing so responsibly:
- Verify the Source: Before turning off Gatekeeper checks for an app, ensure the software comes from a reliable source. Research the developer and the app to confirm its legitimacy and safety.
- Use Manual Overrides Sparingly: Opt for a one-time manual override rather than permanently changing your system’s settings. This minimizes exposure to unverified applications.
- Revert to Default Settings: If you temporarily adjust Gatekeeper’s settings to allow an installation, remember to revert to the more secure default settings immediately afterward.
- Maintain Awareness: Stay informed about the latest security threats and updates to macOS. Regularly updating your system will ensure that Gatekeeper and other security features are equipped to protect against recent vulnerabilities.
By judiciously managing exceptions and employing Gatekeeper’s bypass mechanisms only when necessary, you can maintain an optimal balance between security and functional autonomy on your Mac OS X devices.